Introduction
Part 1: The Basics
Chapter 1: What is Social Engineering?
Chapter 2: Ethical Considerations in Social Engineering
Part 2: Offensive Social Engineering
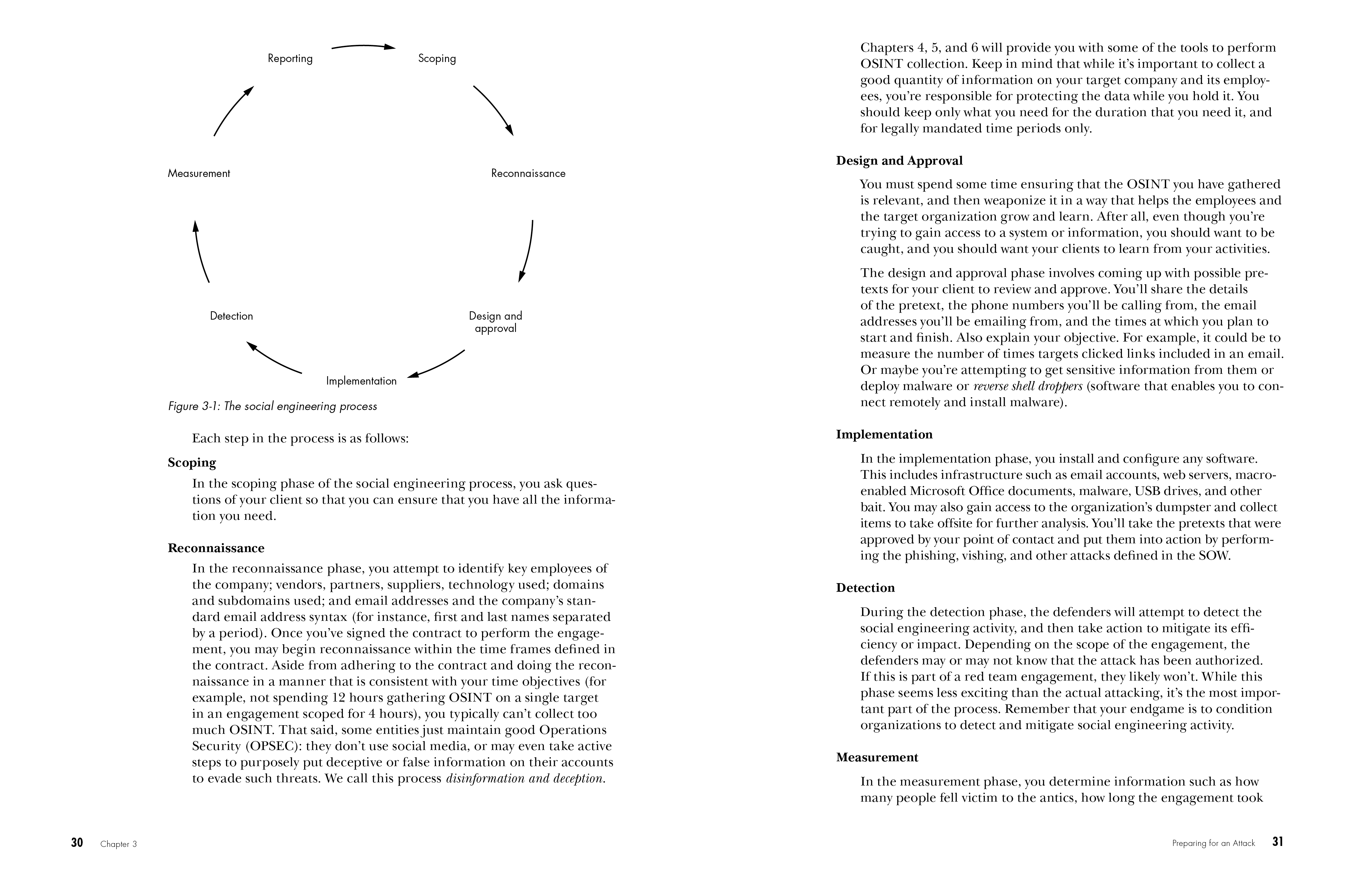
Chapter 3: Preparing for an Attack
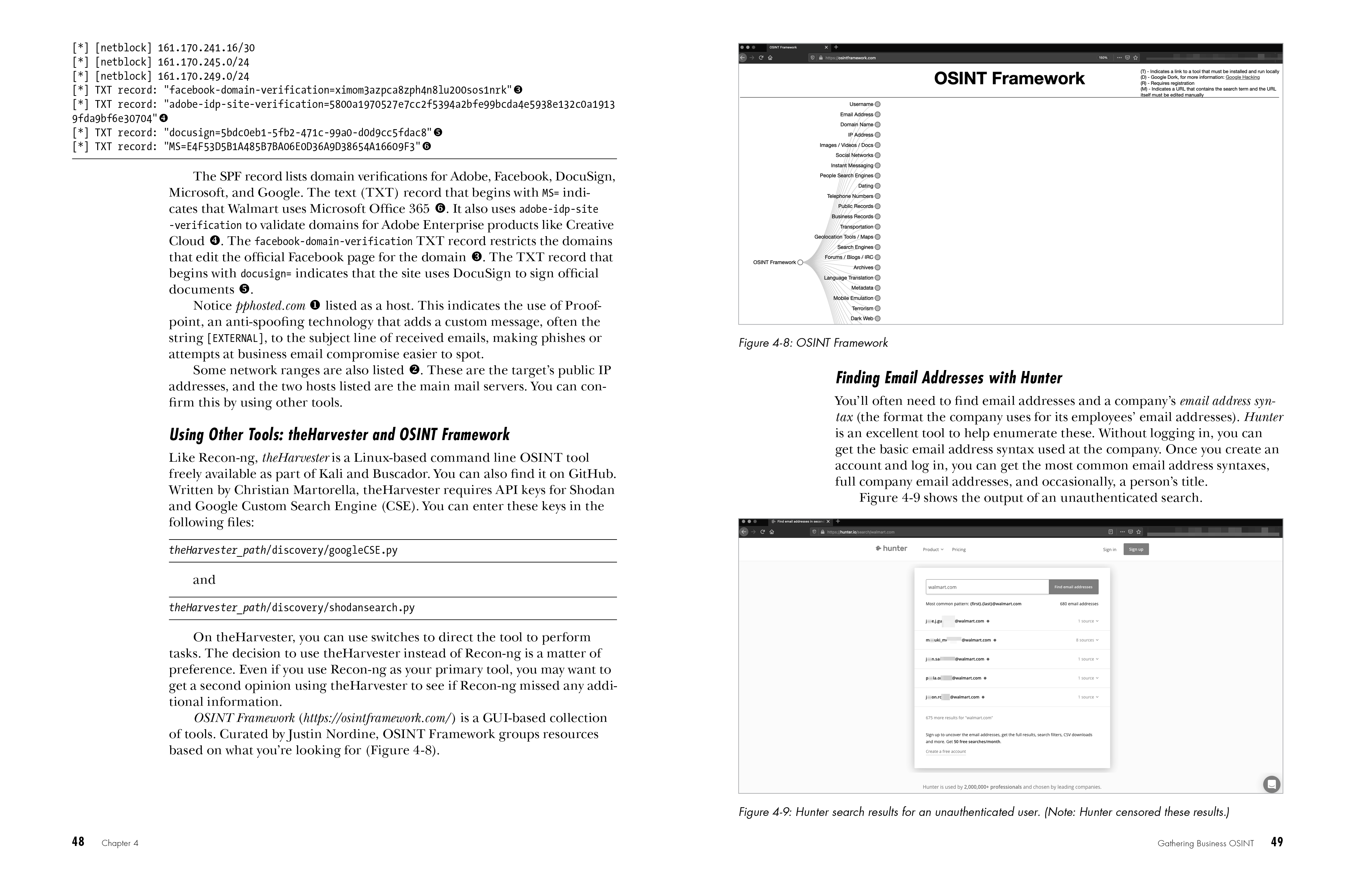
Chapter 4: Gathering Business OSINT
Chapter 5: Social Media and Public Documents
Chapter 6: Gathering OSINT About People
Chapter 7: Phishing
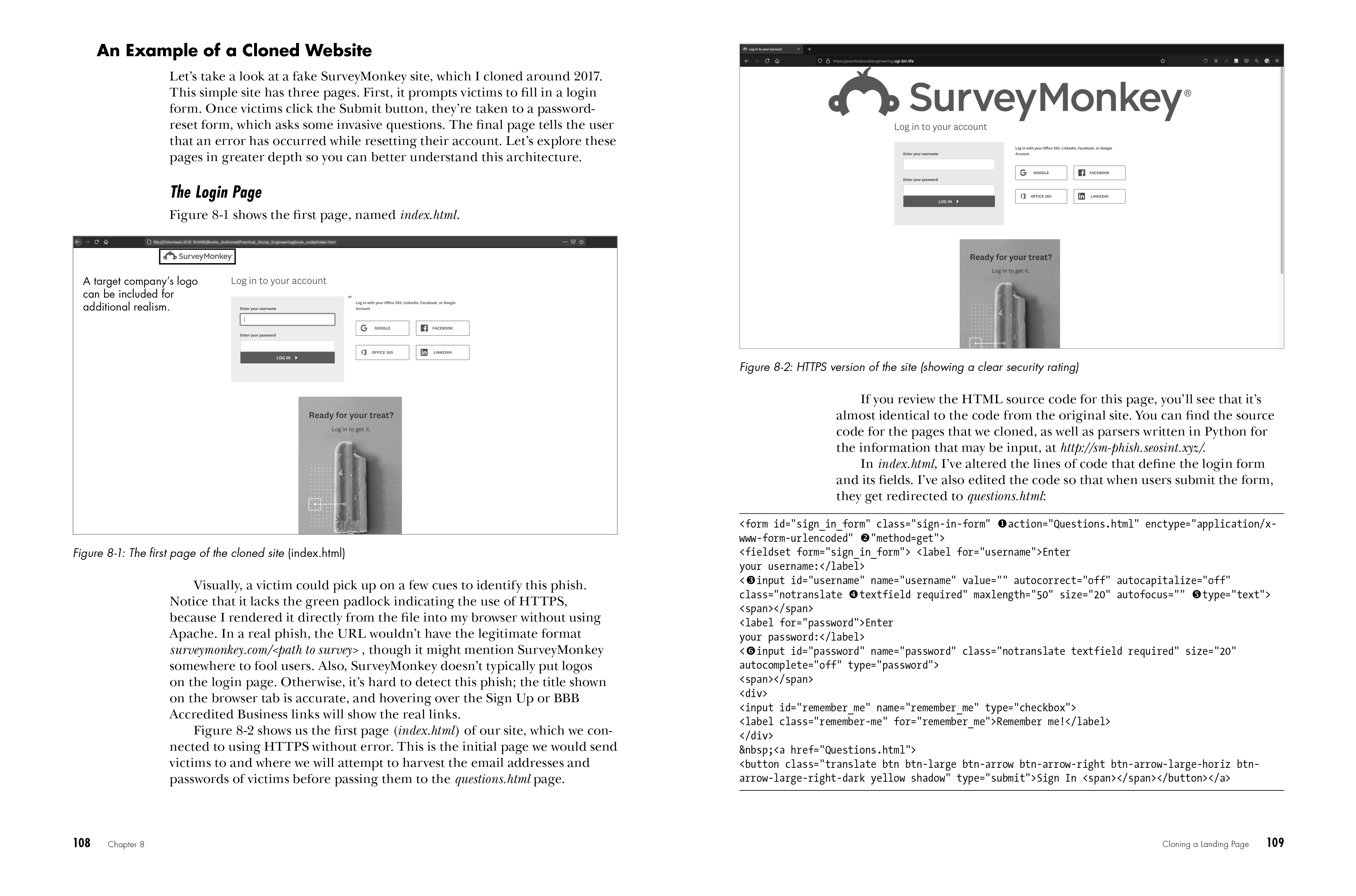
Chapter 8: Cloning a Landing Page
Chapter 9: Detection, Measurement, and Reporting
Part 3: Defending Against Social Engineering
Chapter 10: Proactive Defense Techniques
Chapter 11: Technical Email Controls
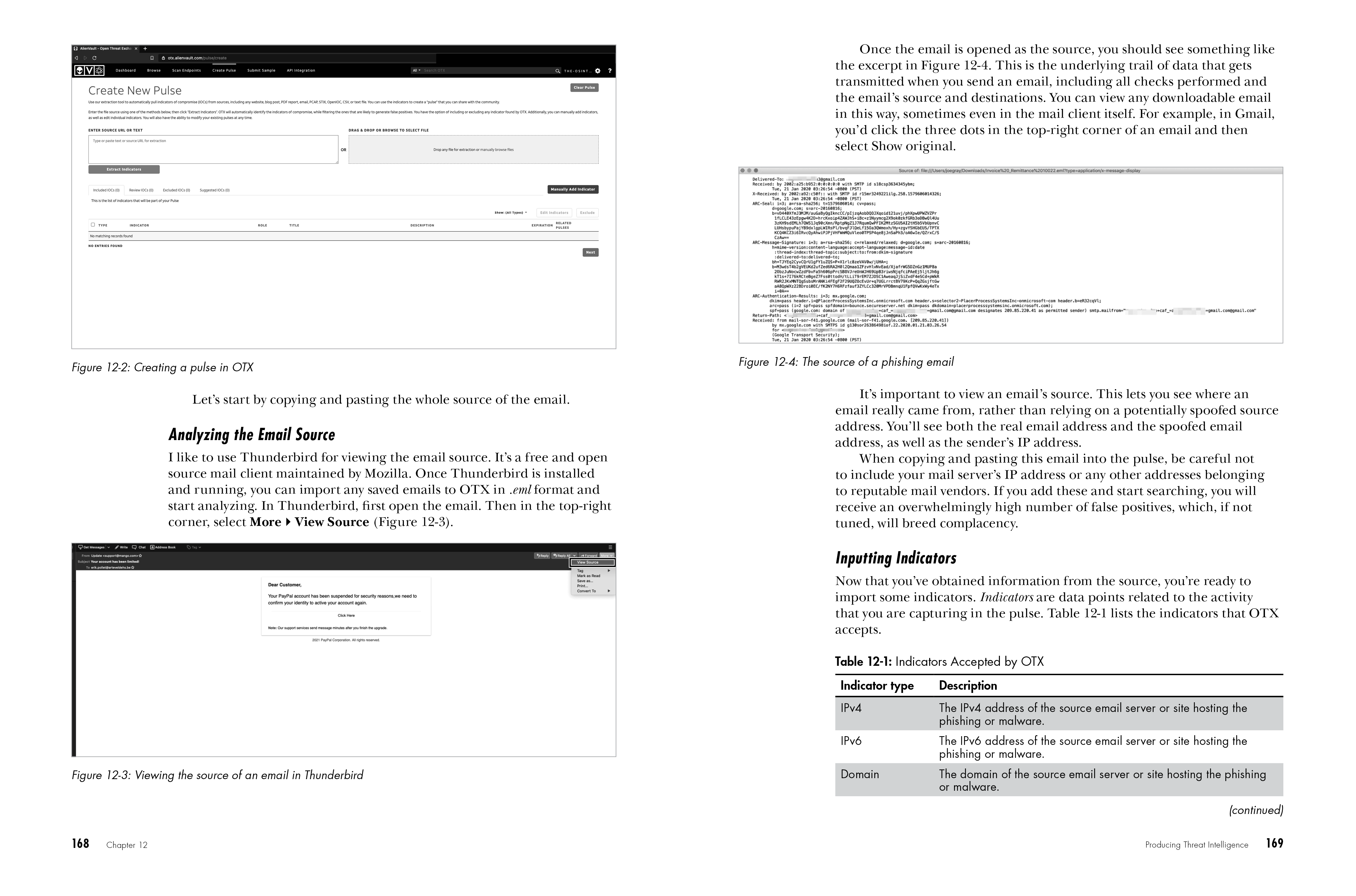
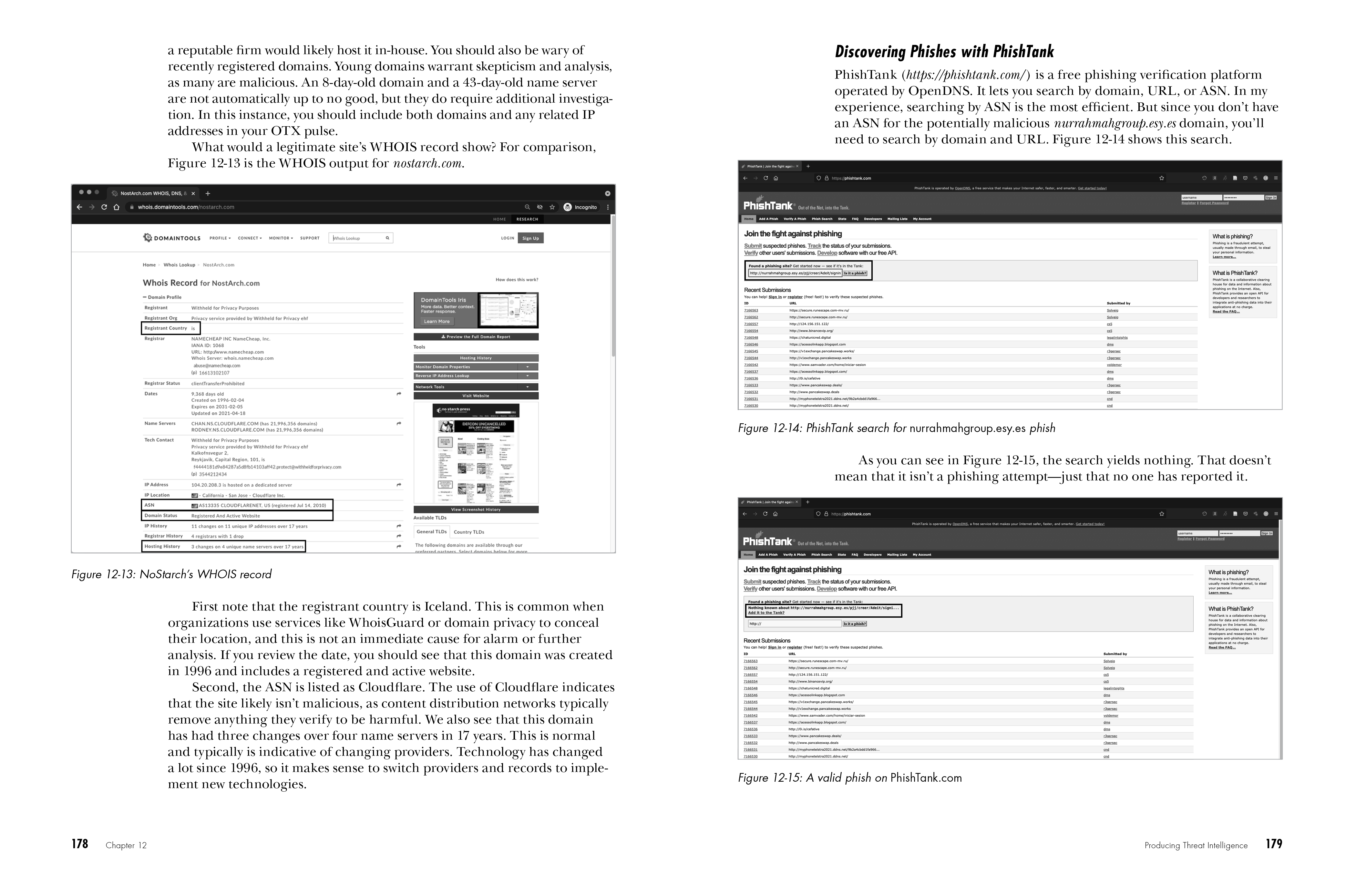
Chapter 12: Producing Threat Intelligence
Appendix A: Scoping Worksheet
Appendix B: Reporting Template
Appendix C: Information Gathering Worksheet
Appendix D: Pretexting Samples
Appendix E: Exercises to Improve Your Social Engineering