Introduction
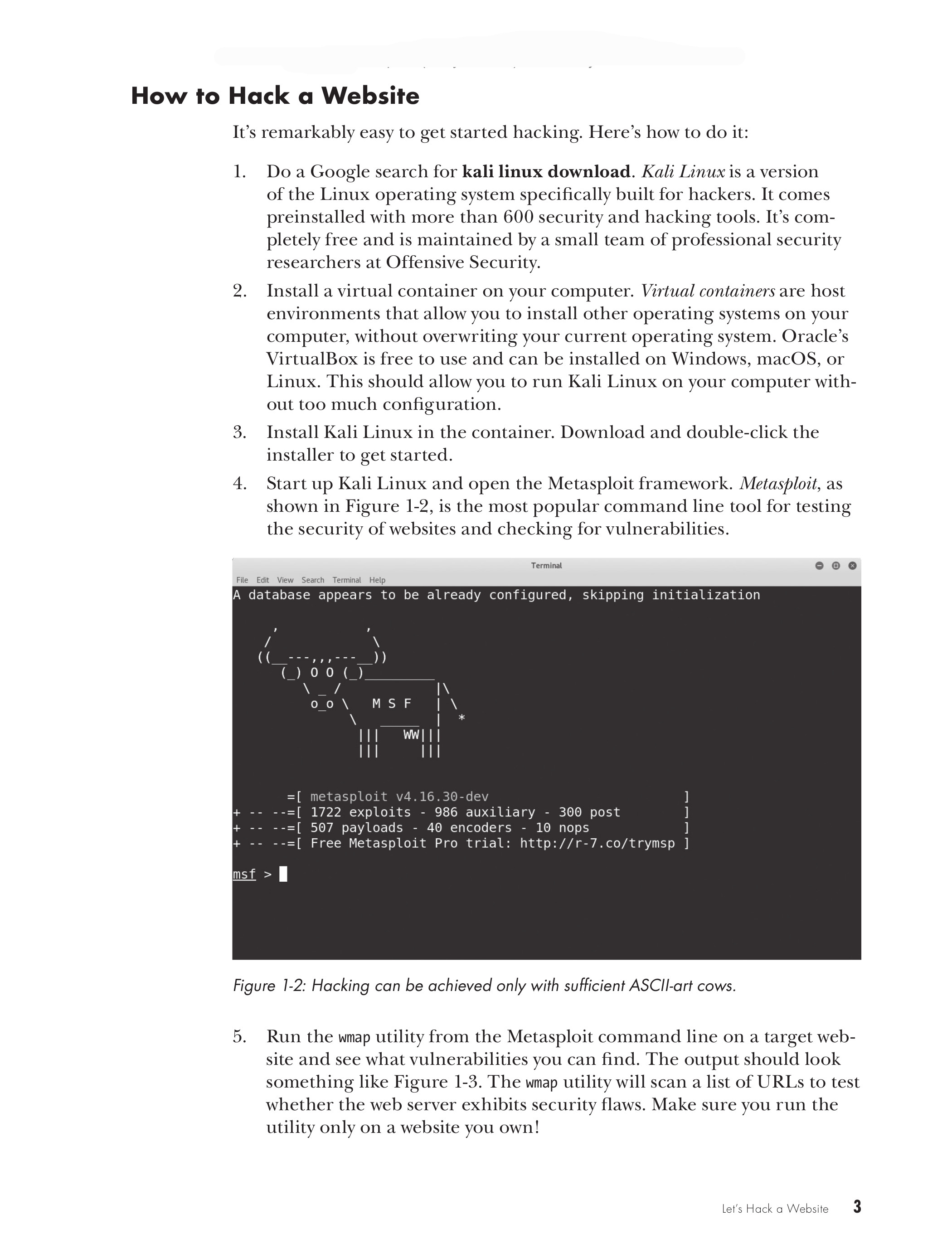
Chapter 1: Let’s Hack a Website
PART I: The Basics
Chapter 2: How the Internet Works
Chapter 3: How Browsers Work
Chapter 4: How Web Servers Work
Chapter 5: How Programmers Work
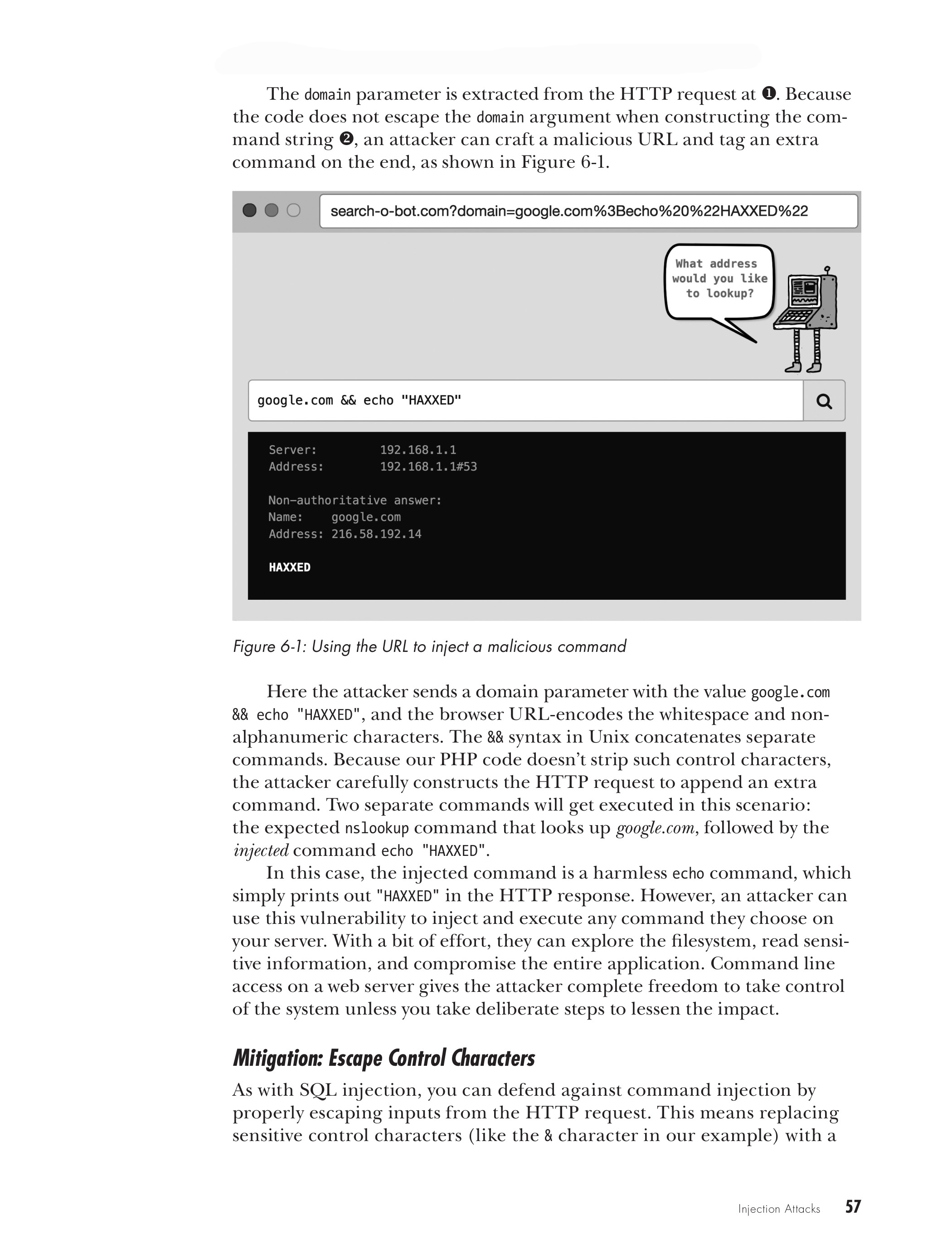
Chapter 6: Injection Attacks
PART II: The Threats
Chapter 7: Cross-Site Scripting Attacks
Chapter 8: Cross-Site Request Forgery Attacks
Chapter 9: Compromising Authentication
Chapter 10: Session Hijacking
Chapter 11: Permissions
Chapter 12: Information Leaks
Chapter 13: Encryption
Chapter 14: Third-party Code
Chapter 15: XML Attacks
Chapter 16: Don't Be an Accessory
Chapter 17: Denial-of-Service Attacks
Chapter 18: Summing Up
Index
Web Security for Developers
Look Inside!
Download Chapter 2: HOW THE INTERNET WORKS
The world has changed. Today, every time you make a site live, you’re opening it up to attack. A first-time developer can easily be discouraged by the difficulties involved with properly securing a website. But have hope: an army of security researchers is out there discovering, documenting, and fixing security flaws. Thankfully, the tools you’ll need to secure your site are freely available and generally easy to use. Web Security for Developers will teach you how your websites are vulnerable to attack and how to protect them. Each chapter breaks down a major security vulnerability and explores a real-world attack, coupled with plenty of code to show you both the vulnerability and the fix. You’ll learn how to:
- Protect against SQL injection attacks, malicious JavaScript, and cross-site request forgery
- Add authentication and shape access control to protect accounts
- Lock down user accounts to prevent attacks that rely on guessing passwords, stealing sessions, or escalating privileges
- Implement encryption
- Manage vulnerabilities in legacy code
- Prevent information leaks that disclose vulnerabilities
- Mitigate advanced attacks like malvertising and denial-of-service
"Reads easily and provides essential knowledge to aspiring web developers." —Help Net Security
"The biggest advantage of this book is that it collects all a developer needs to know in one space....This solid work should be relevant for years to come." —Scott J Pearson
"A good resource for developers at any level to fill in the holes in their knowledge or reinforce their existing expertise." —Jon Lazar
"Lists some cool techniques and also goes deep into some modern internet topics like the deep web. Overall a very fun book to read if you are interested in Web App Security."
—Sudo Realm
"You can frame the usefulness of this book several ways: It’s well suited to those who are transitioning from development to security. It’s also another great security beginner-level read, providing introductions to an array of pen testing tools that will help you do your job better. And finally, it’s a terrific resource for developers looking to build more secure applications."
—Britt Kemp, Bishop Fox Labs
View the latest errata.