Foreword
Introduction
Part I: Fundamentals
Chapter 1: Secure Development Process
Chapter 2: Cryptography
Part II: Device Security Building Blocks
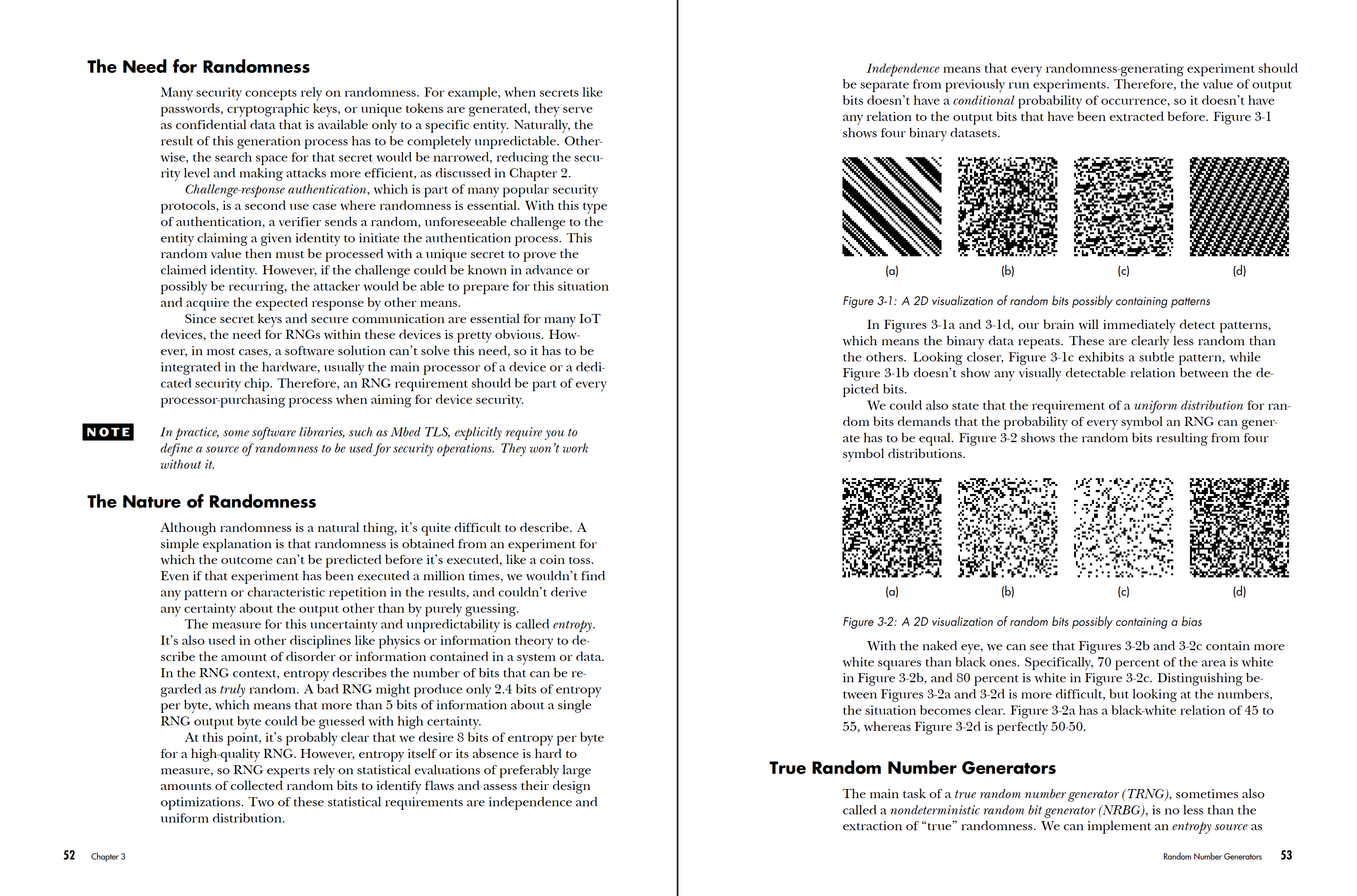
Chapter 3: Random Number Generators
Chapter 4: Cryptographic Implementations
Chapter 5: Confidential Data Storage and Secure Memory
Chapter 6: Secure Device Identity
Chapter 7: Secure Communication
Part III: Advanced Device Security Concepts
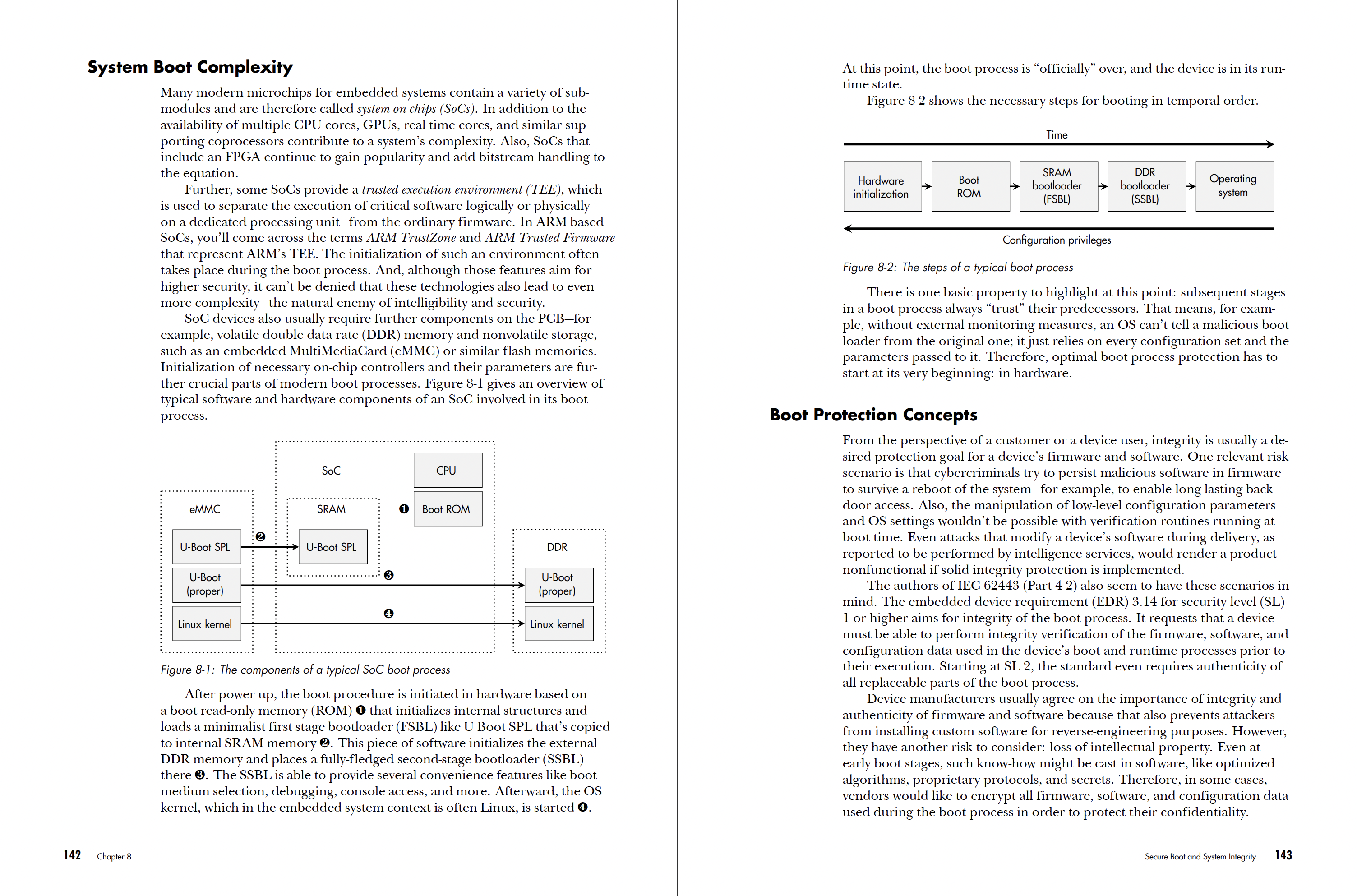
Chapter 8: Secure Boot and System Integrity
Chapter 9: Secure Firmware Update
Chapter 10: Robust Device Architecture
Chapter 11: Access Control and Management
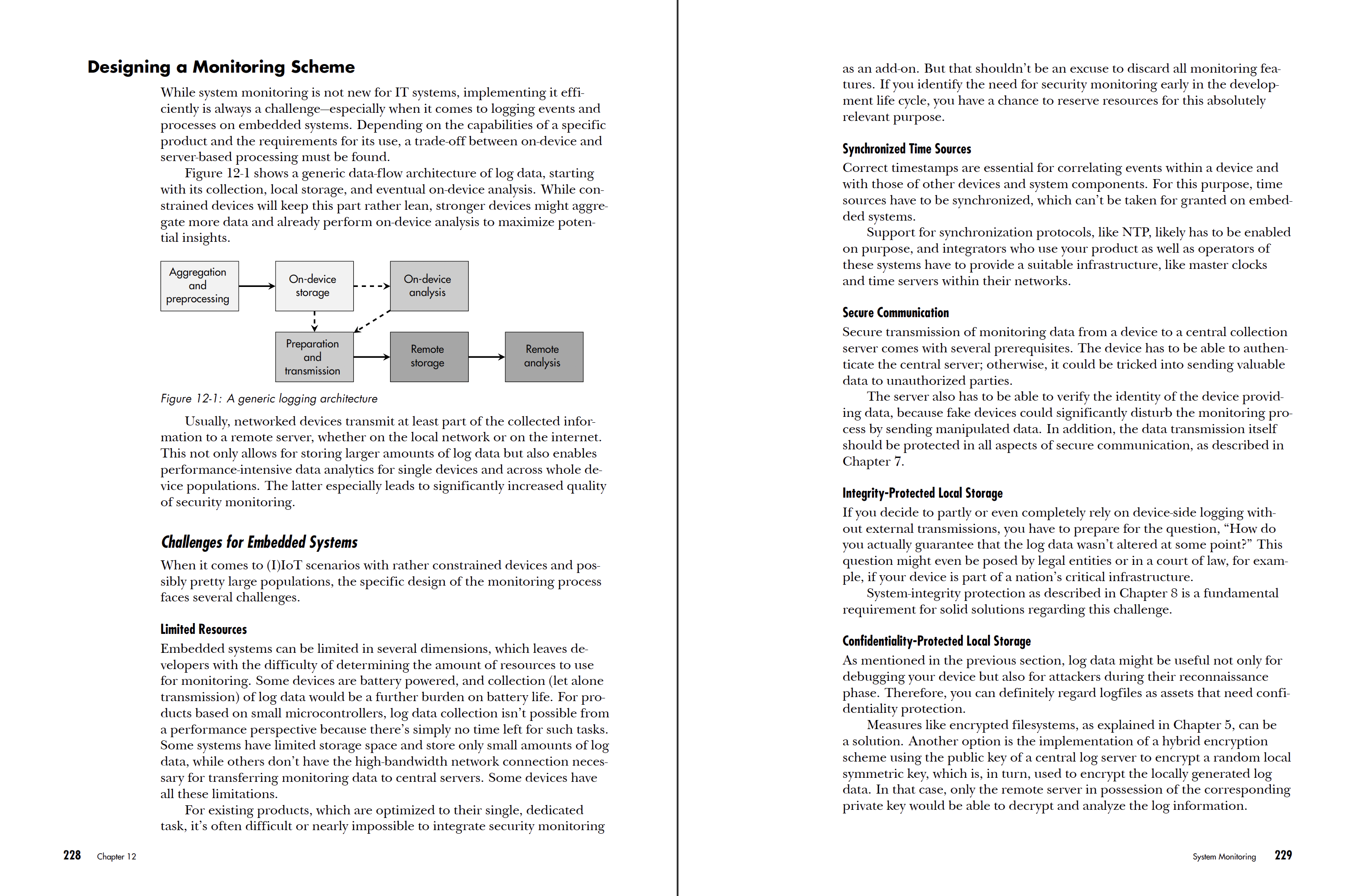
Chapter 12: System Monitoring
Afterword
Index
Engineering Secure Devices
Look Inside!
Download Chapter 6: Secure Device Identity
As an engineer, you know that countless devices—from industrial components to smart household appliances—rely on embedded computer systems. But how do you balance the need for robust security with performance and innovative product design?
Engineering Secure Devices will guide you through crafting secure devices—from protecting crucial assets to the nature of attackers and the risks they pose. You’ll explore the technical intricacies and pros and cons of symmetric and asymmetric cryptography and learn how to use and analyze random number generators and cryptographic algorithms. You’ll learn how to ensure confidential data storage and secure memory, and devise secure device identity solutions and communication protocols to reinforce system architecture against potential threats. And finally, you’ll learn how to properly design secure boot and secure update processes, manage access control, and perform system monitoring to secure IoT devices.
Real-world case studies throughout highlight practical applications, solutions, and obstacles, such as firmware updates with SWUpdate, secure communication with MQTT, and advanced access control with AppArmor.
You’ll also dig into topics like:
- Analyzing the performance of cryptographic implementations in both hardware and software
- Considerations for secure boot and software update processes to ensure ongoing firmware integrity
- Designing robust device architectures that withstand attacks while maintaining critical operations
- Developing strategies to detect and respond to anomalies or security breaches in embedded systems
Whether you’re an IoT developer or an embedded system architect, Engineering Secure Devices equips you with the indispensable knowledge to design, secure, and support the next generation of smart devices—from webcams to four-legged robots.
“The book provides a well understandable introduction on how to design and implement secure embedded devices. Case studies exemplify the practical application of relevant security technologies, making this complex topic well accessible for both practitioners and students.”
—Dr. Rainer Falk, Principal Key Expert for Embedded Security, Siemens AG
“This book has so much valuable and practical information on engineering secure devices with lessons learned by the author and comprehensible case studies. The detailed explanations of security basics and concepts allow the book to be used by beginners to get started on the topic, but even security professionals would definitely find it valuable. Whether you are a developer for an embedded system, responsible for product security, or just interested in the topic, this book is an excellent read!”
—Dr. Matthias Niedermaier, OT Security Expert, Airbus
“This book is an indispensable technical guide for the design, implementation and maintenance of embedded systems in security-sensitive applications. It presents fundamental elements and illustrates how they are utilized in practice, providing seasoned insight into the construction of a secure embedded system.”
—Dr. Marc Stöttinger, Professor of Computer Engineering and Security, RheinMain University of Applied Sciences
“An engaging book for anyone interested in getting a hands-on introduction into embedded system security. Plenty of real-world examples, enriched by anecdotes, make security concepts and mechanisms comprehensible. The book touched on a broad range of topics, encouraging the reader to delve into security engineering.”
—Dr. Johannes Obermaier, security engineer and researcher
"Dominik Merli finally wrote the textbook that everyone teaching on embedded system security was waiting for. The focus on the practical aspects of real-world embedded systems with the relevant theoretical background makes it an excellent base for education and practitioners. I am really excited to use it in my courses."
—Dr. Stefan Wallentowitz, Professor of Embedded System Security, Hochschule München University of Applied Sciences
"This book is exactly what you need to read as an engineer working in the automotive, industrial, or IoT domain to level up with comprehensive security know-how — from secure design processes to comprehensive security concepts and their secure implementations. The scope clearly covers what is needed in practice."
—Dr. Johann Heyszl, Security Engineering Manager, Google
"An excellent book for practitioners dealing with the security of embedded systems and IoT security. A special feature of the book is the large number of practical examples and instructions that help the reader to understand and implement security requirements for embedded systems. Dominik succeeds in converting his extensive practical knowledge into an exciting book that can be used both to familiarize yourself with the complex topic and also as a reference."
—Wolfgang Rankl, author of The Smart Card Handbook
"Engineering Secure Devices offers modern, secure product-development lifecycle practices and principles mixed with adversarial perspectives rounding out risk considerations for readers. You’ll find robust and proven product security concepts used to anchor trust in a device’s platform architecture, paired with case study walk-throughs."
—Aaron Guzman, Head of Trust Assurance, Cisco Meraki