Acknowledgements
Introduction
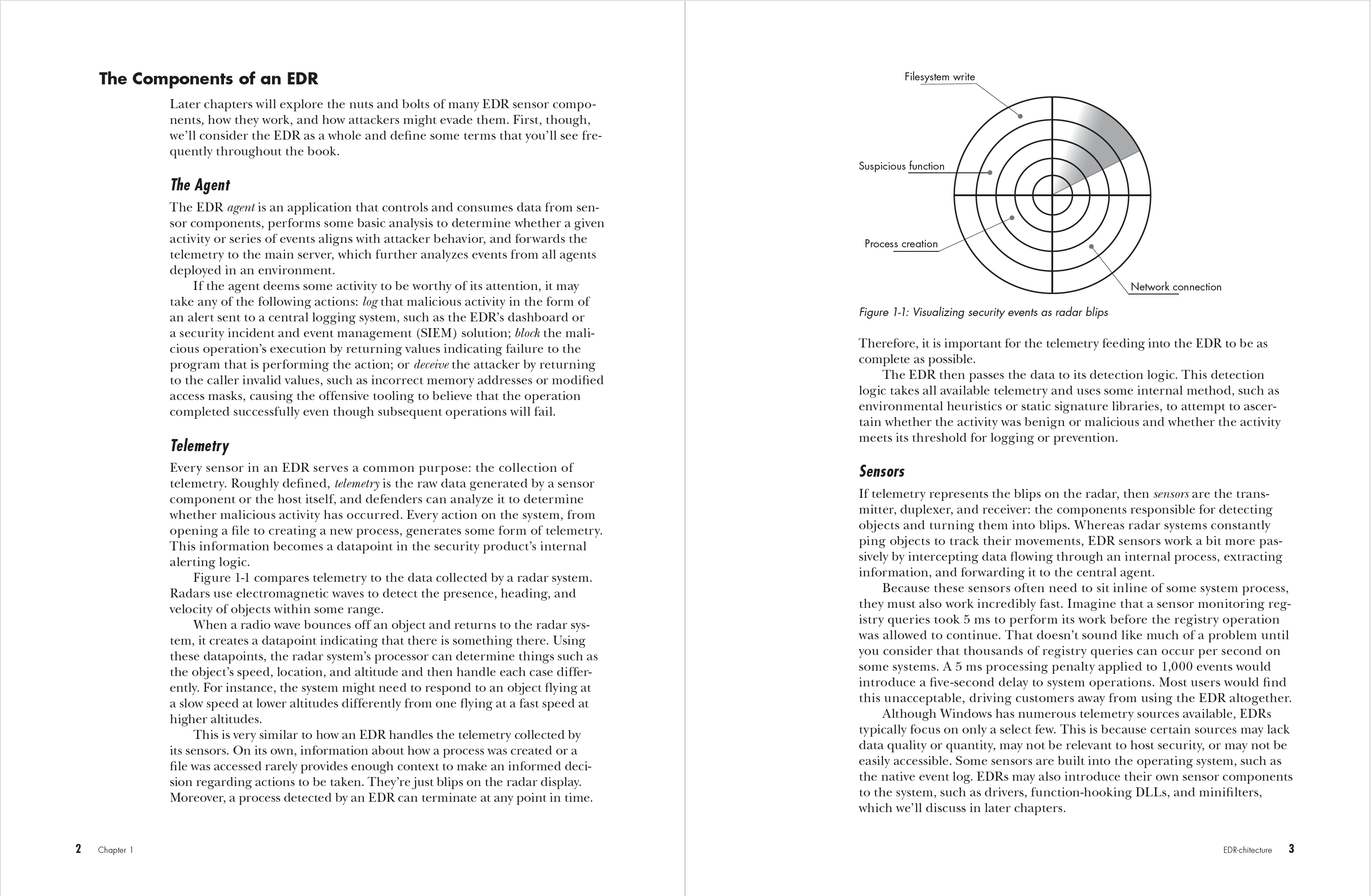
Chapter 1: EDR-chitecture
Chapter 2: Function-Hooking DLLs
Chapter 3: Process- and Thread-Creation Notifications
Chapter 4: Object Notifications
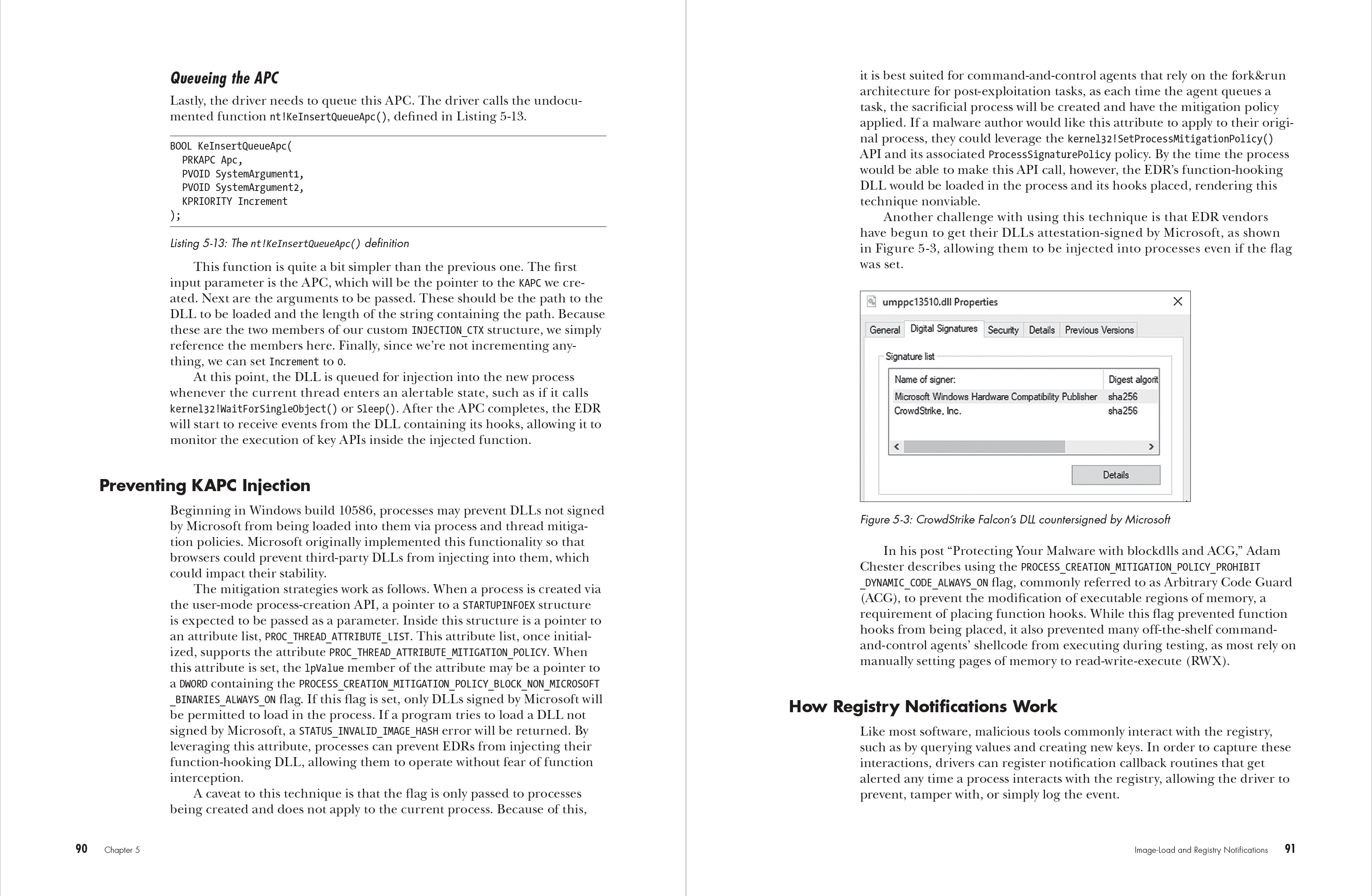
Chapter 5: Image-Load and Registry Notifications
Chapter 6: Filesystem Minifilter Drivers
Chapter 7: Network Filter Drivers
Chapter 8: Event Tracing for Windows
Chapter 9: Scanners
Chapter 10: Anti-Malware Scan Interface
Chapter 11: Early Launch Antimalware Drivers
Chapter 12: Microsoft-Windows-Threat-Intelligence
Chapter 13: Case Study: A Detection-Aware Attack
Appendix: Auxiliary Sources
View the Copyright page
View the detailed Table of Contents
View the Index