Introduction
Chapter 1: Getting Started with a Base Linux System and Network Map
Chapter 2: Architecting and Segmenting Your Network
Chapter 3: Filtering Network Traffic with Firewalls
Chapter 4: Securing Wireless Networks
Chapter 5: Creating a Virtual Private Network
Chapter 6: Improving Browsing and Privacy with the Squid Proxy
Chapter 7: Blocking Internet Advertisements
Chapter 8: Detecting, Preventing, and Removing Malware
Chapter 9: Backing Up Your Data
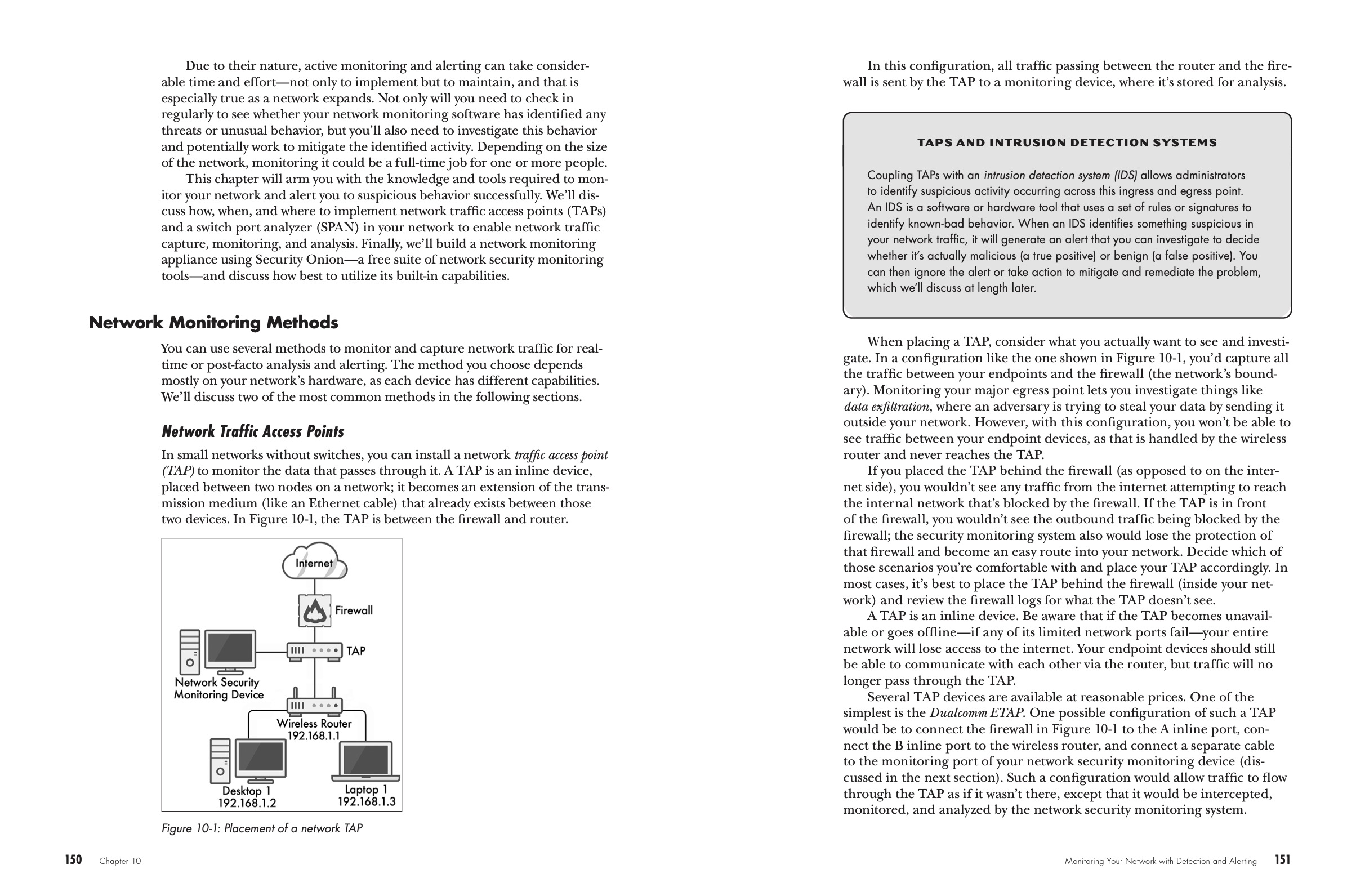
Chapter 10: Monitoring Your Network with Detection and Alerting
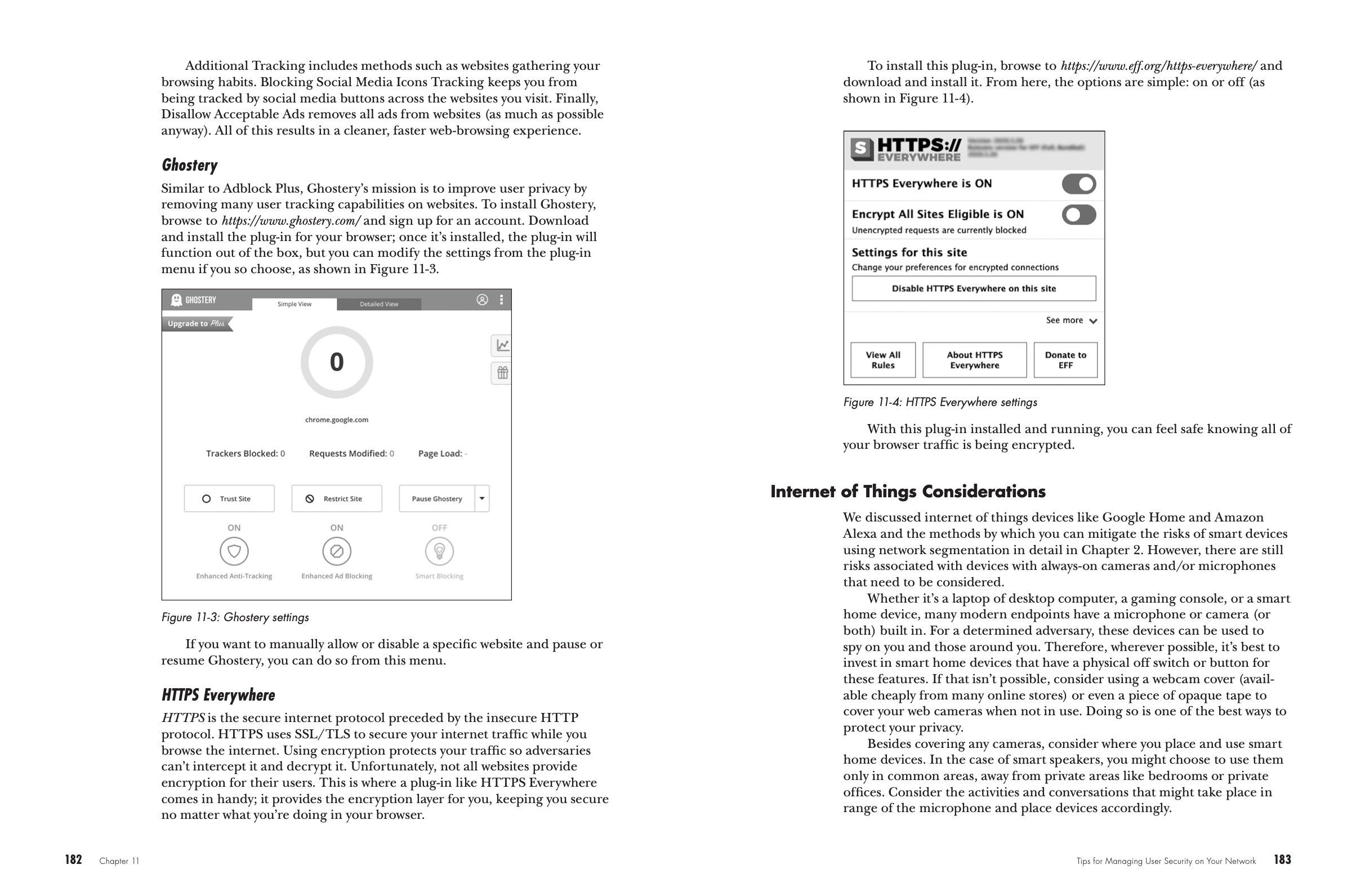
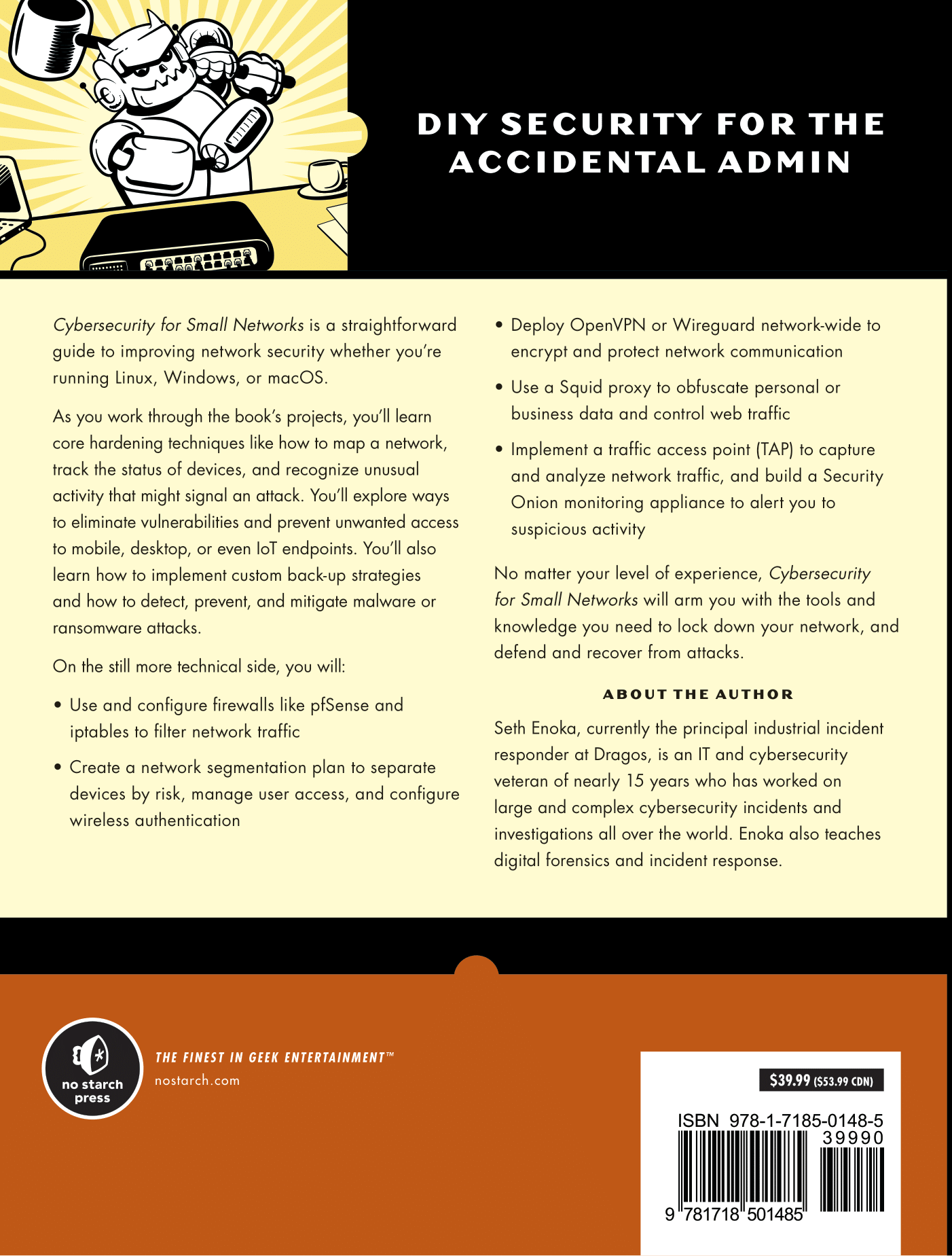
Chapter 11: Tips for Managing User Security on Your Network
View the Copyright page
View the detailed Table of Contents
View the Index