Foreword
Acknowledgments
Introduction
Part I
Chapter 1. Setting Up a PowerShell Testing Environment
Chapter 2. The Windows Kernel
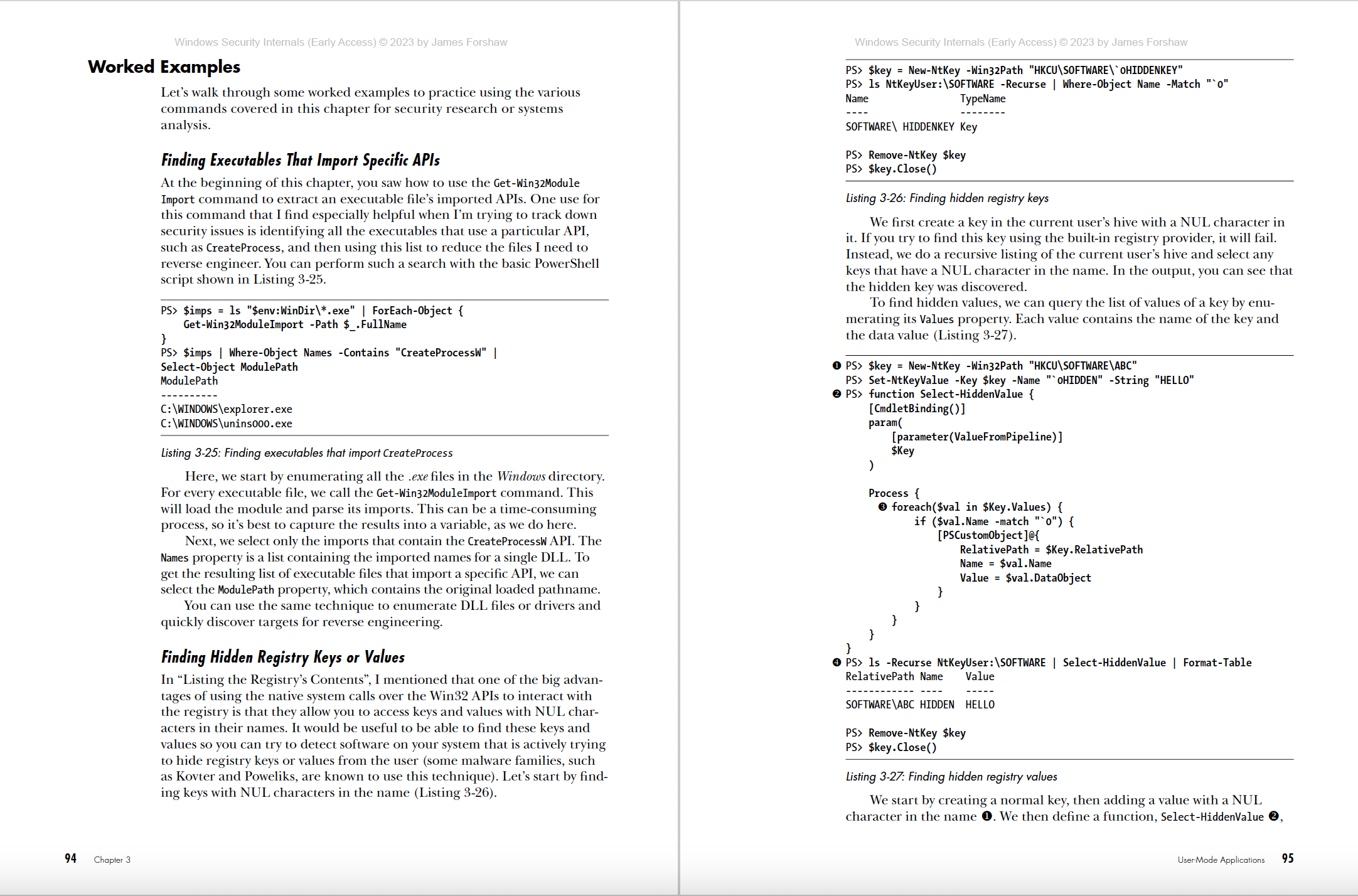
Chapter 3. User-Mode Applications
Part II
Chapter 4. Security Access Tokens
Chapter 5. Security Descriptors
Chapter 6. Reading and Assigning Security Descriptors
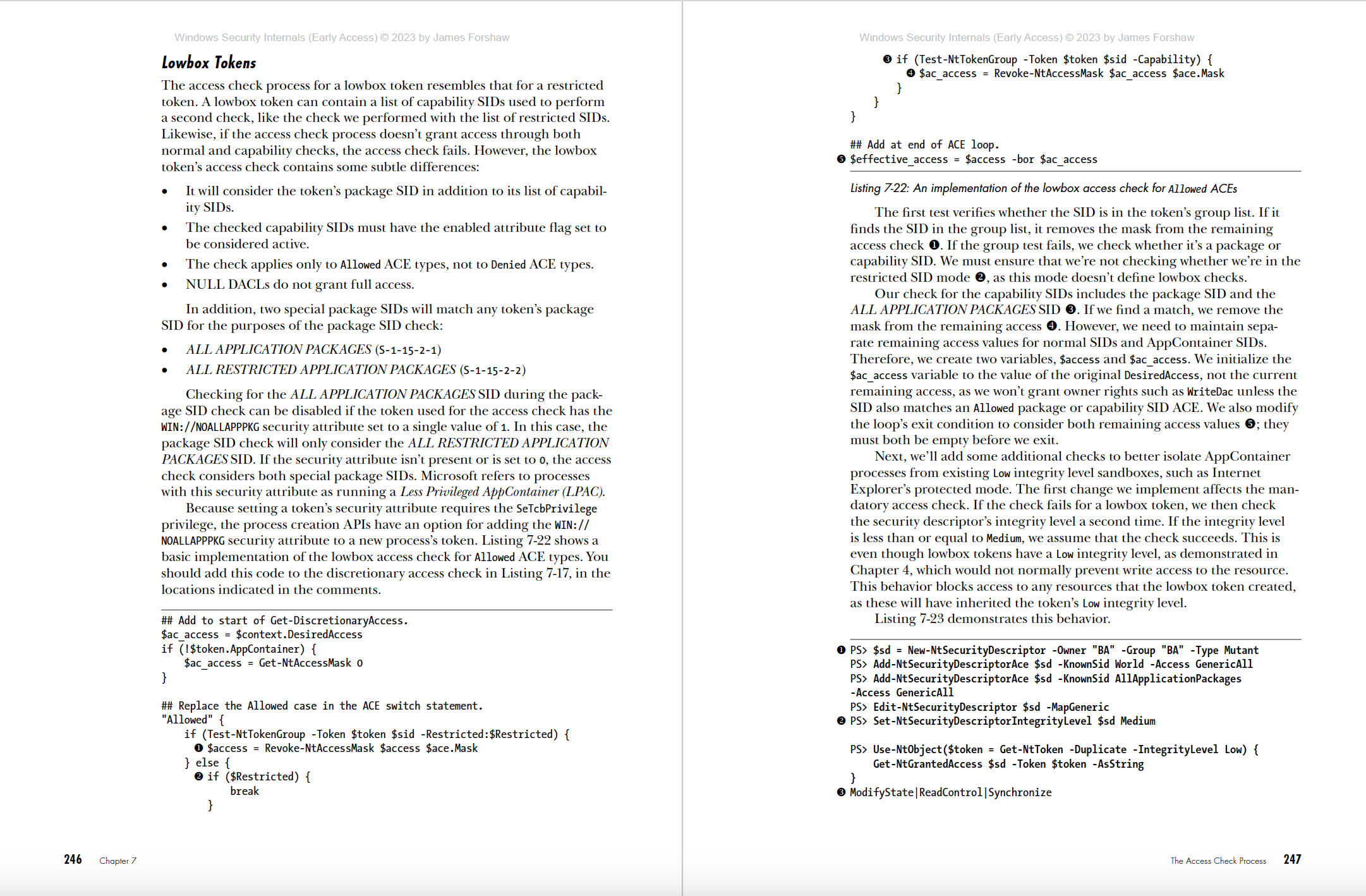
Chapter 7. Access Checking
Chapter 8. Other Access Checking Use Cases
Chapter 9. Security Auditing
Part III
Chapter 10. Windows Authentication
Chapter 11. Active Directory
Chapter 12. Interactive Authentication
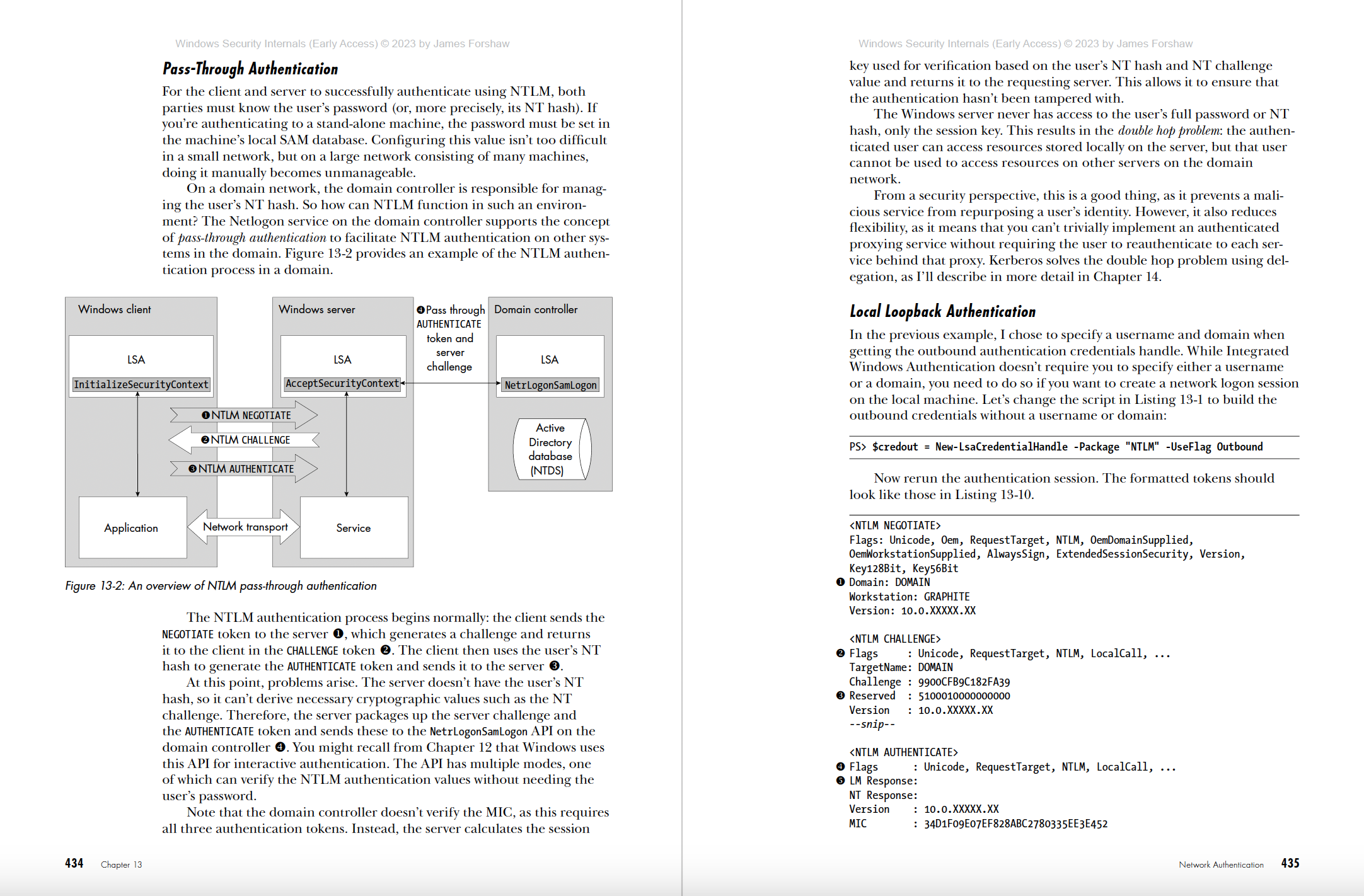
Chapter 13. Network Authentication
Chapter 14. Kerberos
Chapter 15. Negotiate Authentication and Other Security Packages
Appendix A: Building a Windows Domain Network for Testing
Appendix B: SDDL SID Alias Mapping
Index
View the Copyright page
View the detailed Table of Contents
View the Index