Introduction
Part I: An Advanced Cyber Threat Landscape
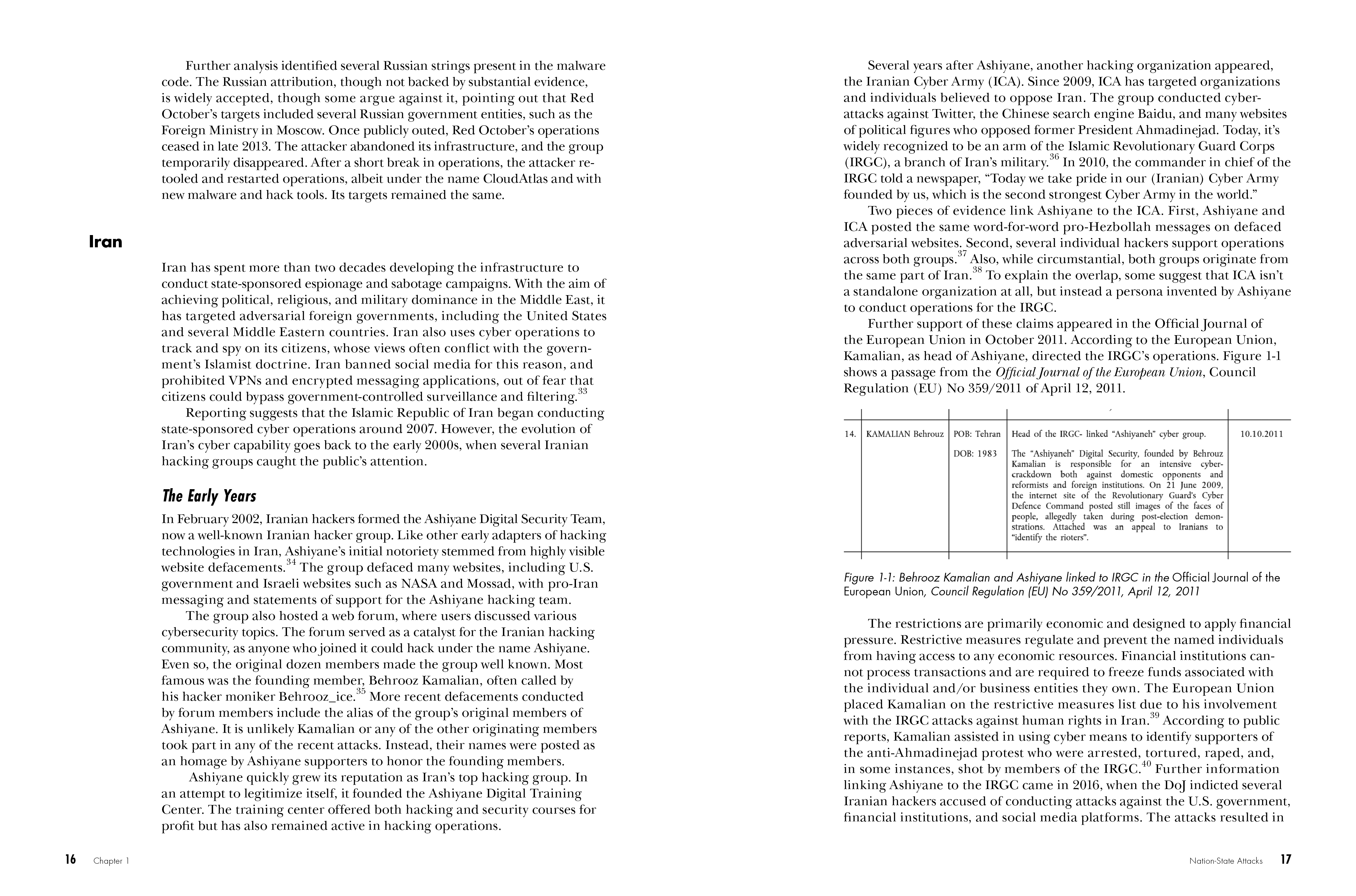
Chapter 1: Nation-State Attacks
Chapter 2: State-Sponsored Financial Attacks
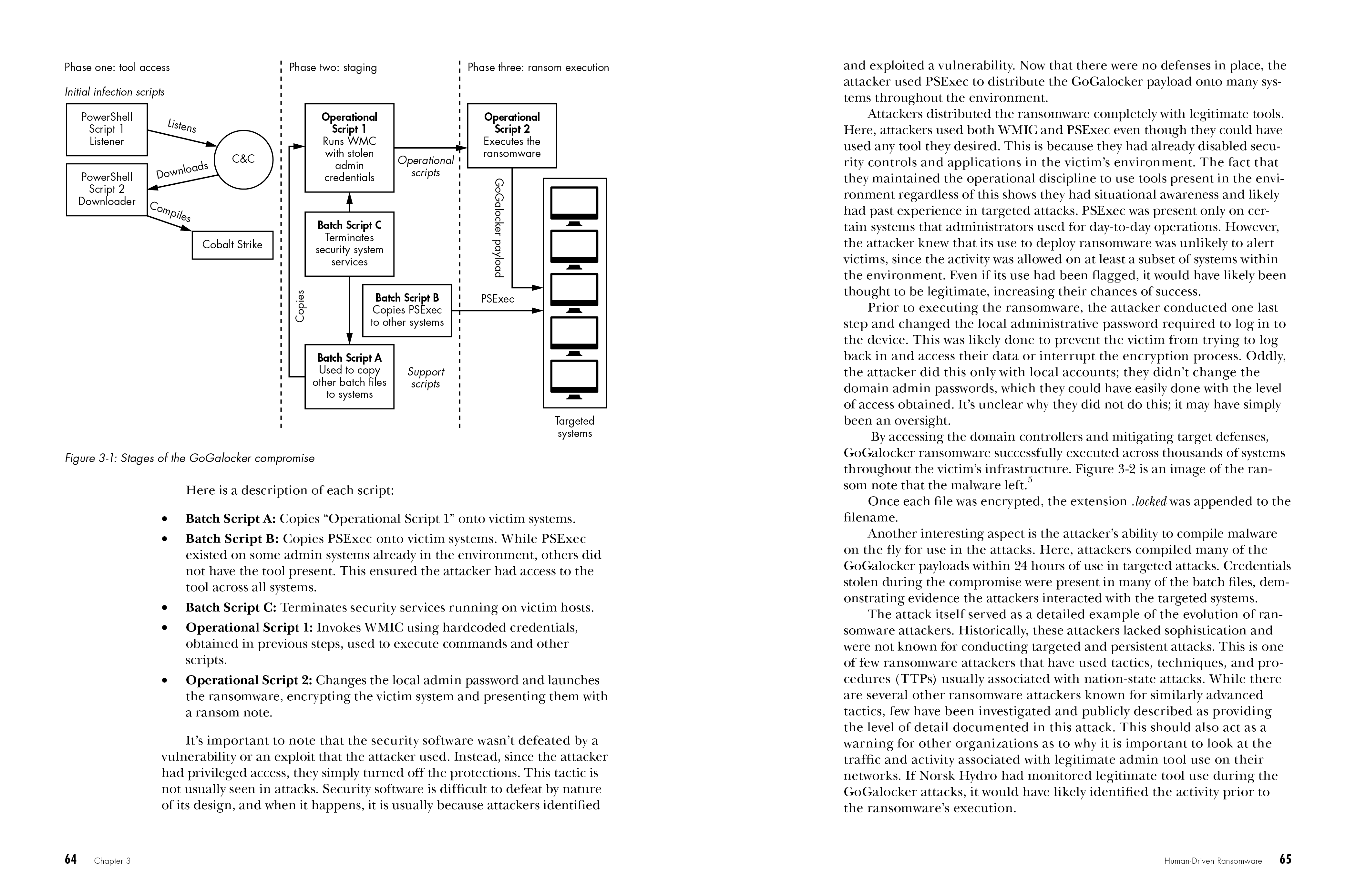
Chapter 3: Human-Driven Ransomware
Chapter 4: Election Hacking
Part II: Hunting and Analyzing Advanced Cyber Threats
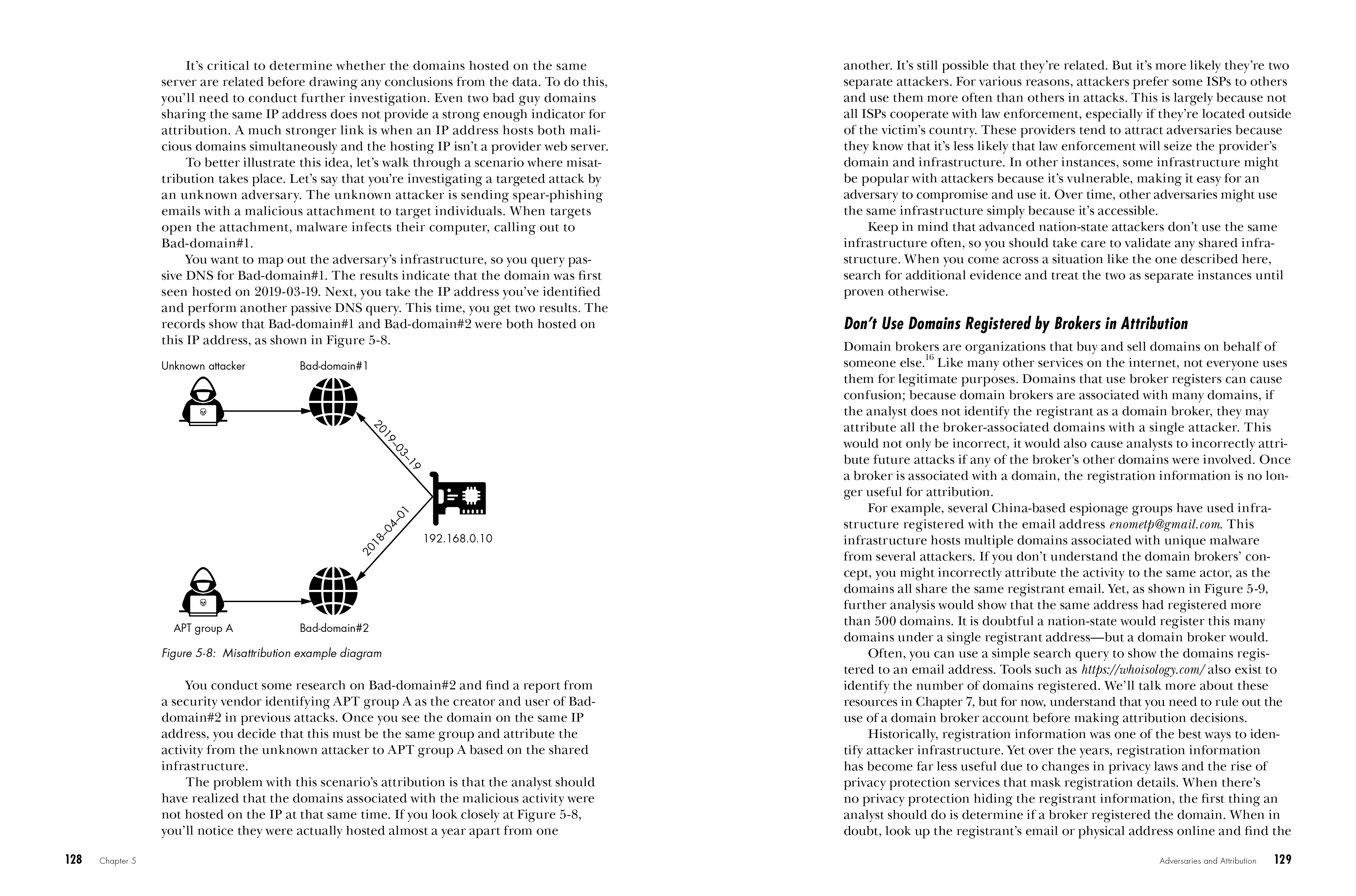
Chapter 5: Analysis and Attribution
Chapter 6: Malware Distribution and Communication
Chapter 7: Open Source Threat Hunting
Chapter 8: Analyzing a Real-World Threat
Endnotes
Appendix A: Threat Profile Questions
Appendix B: Threat Profile Template Example