Download Chapter 2: PERSISTENCE
Look Inside!
Defenders must fully understand how malicious software works if they hope to stay ahead of the increasingly sophisticated threats facing Apple products today. The Art of Mac Malware, Volume 1: The Guide to Analyzing Malicious Software is a comprehensive handbook to cracking open these malicious programs and seeing what’s inside. Discover the secrets of nation state backdoors, destructive ransomware, and subversive cryptocurrency miners as you uncover their infection methods, persistence strategies, and insidious capabilities. Then work with and extend foundational reverse-engineering tools to extract and decrypt embedded strings, unpack protected Mach-O malware, and even reconstruct binary code. Next, using a debugger, you’ll execute the malware, instruction by instruction, to discover exactly how it operates. In the book’s final section, you’ll put these lessons into practice by analyzing a complex Mac malware specimen on your own. You’ll learn to:
- Recognize common infections vectors, persistence mechanisms, and payloads leveraged by Mac malware
- Triage unknown samples in order to quickly classify them as benign or malicious
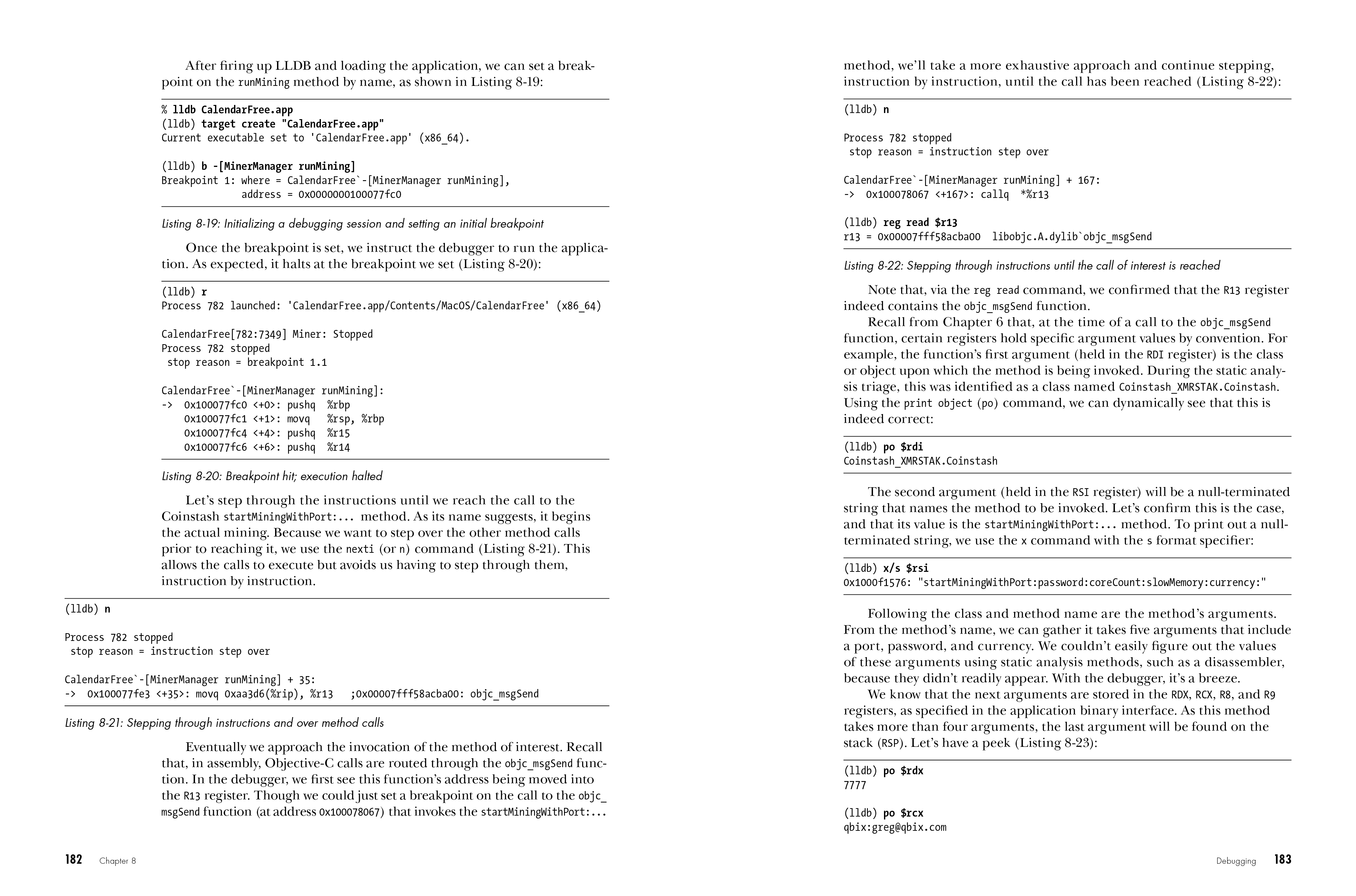
- Work with static analysis tools, including disassemblers, in order to study malicious scripts and compiled binaries
- Leverage dynamical analysis tools, such as monitoring tools and debuggers, to gain further insight into sophisticated threats
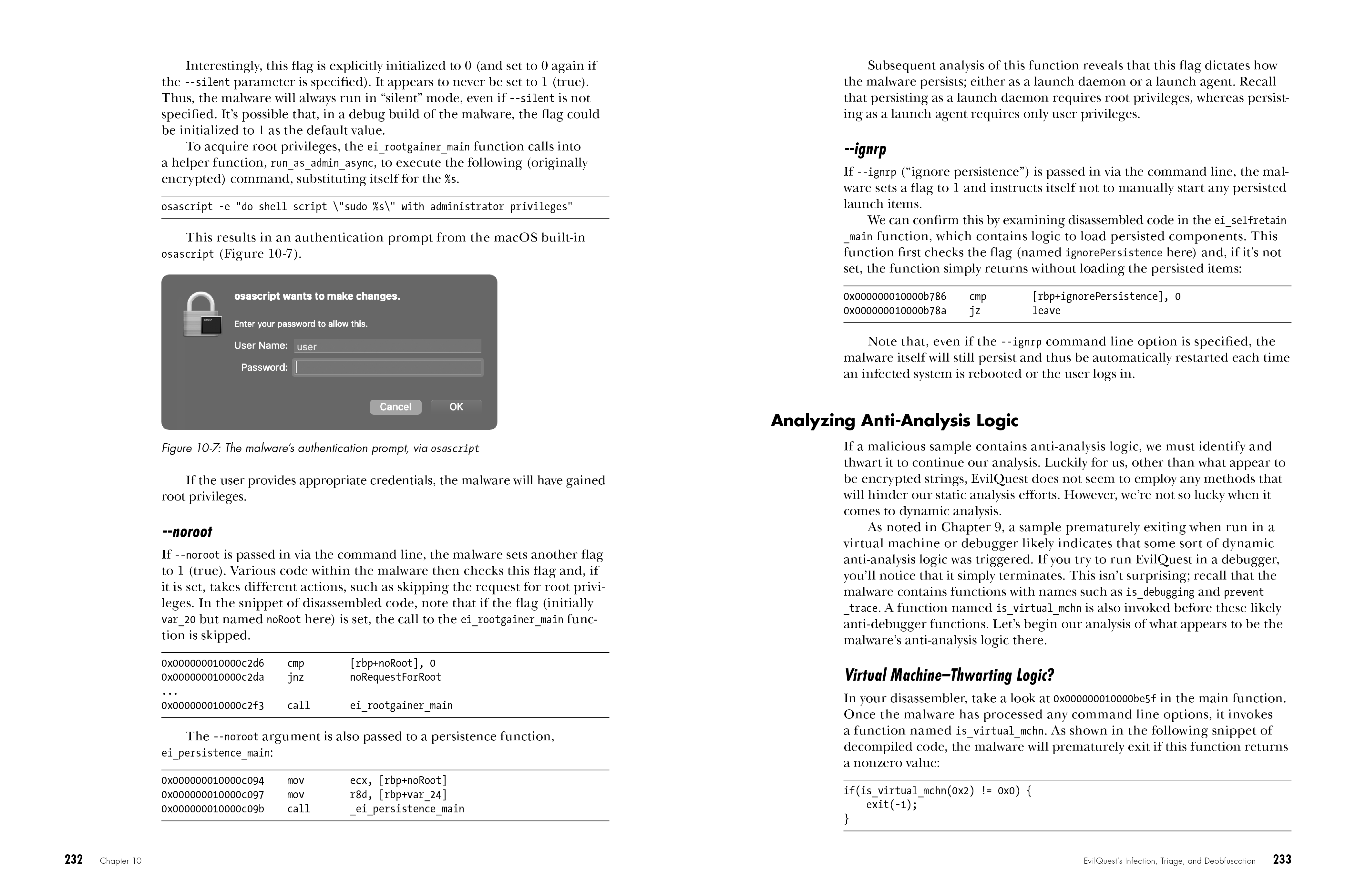
- Quickly identify and bypass anti-analysis techniques aimed at thwarting your analysis attempts
A former NSA hacker and current leader in the field of macOS threat analysis, Patrick Wardle uses real-world examples pulled from his original research. The Art of Mac Malware, Volume 1: The Guide to Analyzing Malicious Software is the definitive resource to battling these ever more prevalent and insidious Apple-focused threats.
Find Volume 2, Detecting Malicious Software, here.