Introduction
14 High Five to the Heavens
14:02 Z-Ring Phreaking by Vicki Pfau
14:03 Concerning Desert Studies by Manul Laphroaig
14:04 Texting with Flush+Reload by Taylor Hornby
14:05 Anti-Keylogging with Noise by Mike Myers
14:06 Random NOPs in ARM by Timmers and Spruyt
14:07 Ethernet Over GDB by Micah Elizabeth Scott
14:08 Control Panel Vulnerabilities by Geoff Chappell
14:09 Hash Function Pseudo-Fixpoints by Greg Kopf
14:10 A PDF That Shows Its Own MD5 by Mako
14:11 A GIF shows its own MD5! by Kristoffer “spq” Janke
14:12 MD5 NES Polyglot by Evan Sultanik and Evan Teran
15 I Slipped a Little
15:02 Pier Solar and the Great Reverser by Brandon L. Wilson
15:03 The Alternator Sermon by Manul Laphroaig
15:04 Text2Com by Saumil Shah
15:05 RISC-V Shellcode by Don A. Bailey
15:06 Cracking Gumball by 4am and Peter Ferrie
15:07 A PDF that is a Git Repo by Evan Sultanik
15:08 Zero Overhead Networking by Robert Graham
15:09 Detecting MIPS16 Emulation by Goodspeed and Speers
15:10 Tracing Race Conditions by BSDaemon and NadavCh
15:11 x86 without Data Fetches by Chris Domas
15:12 Java Key Store’s Coffin by Tobias “floyd” Ospelt
15:13 The PNG Gamma Trick by Hector Martin ‘marcan’
16 Laphroaig Races the Runtime Relinker
16:02 Sapere aude! by Manul Laphroaig
16:03 Emulating my Chevy by Brandon L. Wilson
16:04 Wafer Thin Locks by Deviant Ollam
16:05 Uses for Useless Bugs by EA
16:06 Fragmented Chunks by Yannay Livneh
16:07 Executing Unmapped Thumb by Maribel Hearn
16:08 Naming Network Interfaces by Cornelius Diekmann
16:09 Obfuscation via Symbolic Regression by JBS
16:10 Stack Return Addresses from Canaries by Matt Davis
16:11 Rescuing Orphans in Thumb2 by T. Goodspeed
16:12 This PDF Reverse Engineers Itself by Evan Sultanik
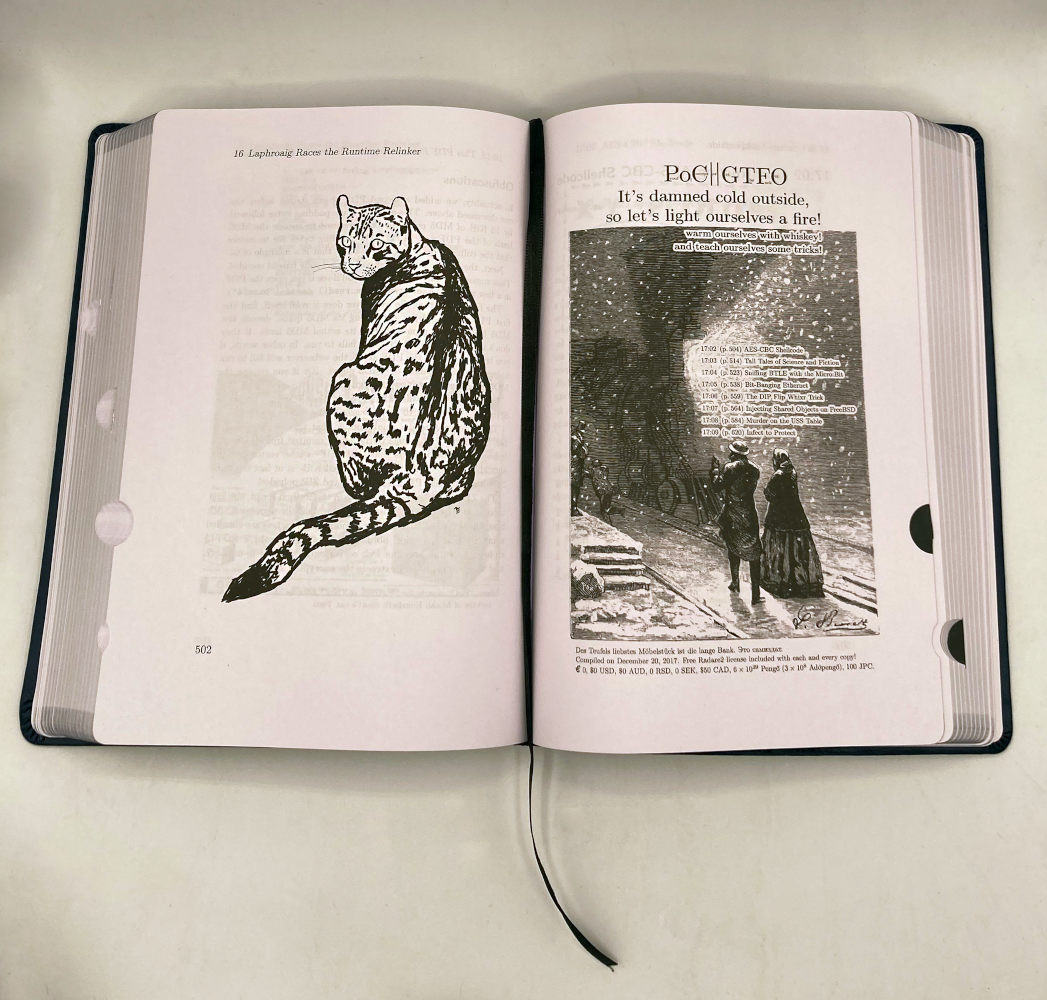
17 It’s damned cold outside
17:02 AES-CBC Shellcode by Spruyt and Timmers
17:03 Tall Tales of Science and Fiction by PML
17:04 Sniffing BTLE with the Micro:Bit by Damien Cauquil
17:05 Bit-Banging Ethernet by Andrew Zonenberg
17:06 The DIP Flip Whixr Trick by Joe Grand
17:07 Injecting Shared Objects on FreeBSD by Shawn Webb
17:08 Murder on the USS Table by Soldier of Fortran
17:09 Infect to Protect by Leandro Pereira
18 Montessori Soldering School
18:02 An 8 Kilobyte Mode 7 Demo by Vincent Weaver
18:03 Exploits for Kids with Scratch! by Kev Sheldrake
18:04 Concealing ZIP Files in NES Cartridges by Vi Grey
18:05 House of Fun by Yannay Livneh
18:06 Read Only Relocations for Static ELF by Ryan O’Neill
18:07 Remotely Exploiting Tetrinet by Laky and Hanslovan
18:08 KLEE Internals by Julien Vanegue
18:09 Reversing DDR3 Scrambling by Nico Heijningen
18:10 SHA-1 Collisions with PDFLaTeX by Ange Albertini
Useful Tables
Index
Colophon