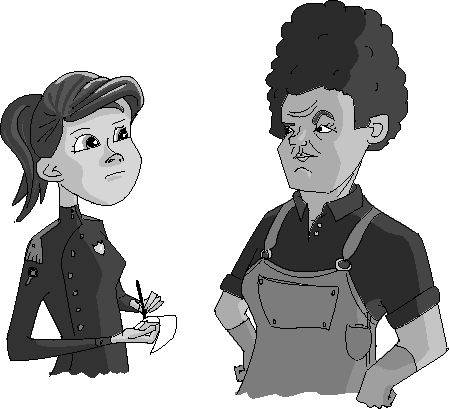
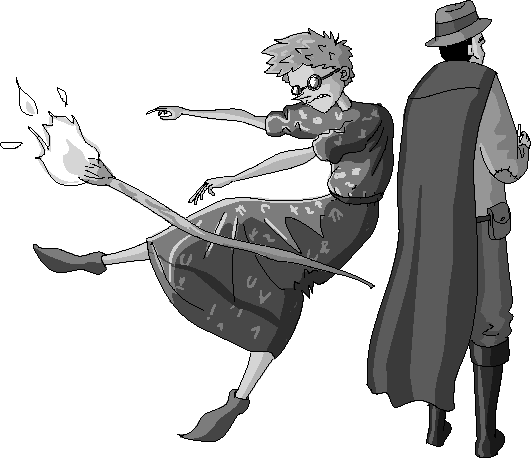
The door opened without a knock—only the hinge’s creak announced the visitor. Frank started for his crossbow, but pulled up short. If the Vinettees were coming for him, they would have knocked—with an axe. Whoever was coming through the door must want to talk. Frank reached for his mug instead and downed the remainder of his now-cold coffee.
“Captain Donovan,” he said as the man entered. “What brings you to this fine neighborhood? I thought you didn’t venture below Fifteenth Street anymore.”
“It’s been a while,” the captain said simply. “How’ve you been, Frank?”
“Spectacular,” Frank answered dryly, eyeing the captain as he walked a slow circuit around the room.
Donovan scanned Frank’s shabby office. His red officer’s cloak swished gently behind him. “How’s the private eye game?”
“It pays the bills,” Frank lied.
The captain nodded. He paused for a moment, then moved to the bookshelf and browsed the contents.
“So is this a social visit then?” Frank said. “Should I be asking after Marlene and the kids?”
“They’re quite well,” replied Donovan without turning around. “Marlene’s turtle-grooming business is doing well these days. Bill joined the force last year. And Veronica is an accountant, just about the last thing we would have—”
“I wasn’t actually asking,” Frank interrupted.
The captain shrugged. He pulled a book from the shelf and leafed through the pages. Frank craned his neck to see the cover—Police Academy Yearbook: Class XXI.
“What do you want, Captain?” Frank demanded.
The captain met Frank’s stare at last. “I need your help, Frank,” he said.
Frank straightened. In the five years since Frank had left the force, the captain had paid him exactly two visits, and both had been to warn him to stay away from active cases. Threats were all Frank had come to expect, but now it seemed the captain had a special kind of problem—perhaps the kind that would mean an end to Frank’s delinquent rent.
“I’m not on the force anymore,” said Frank airily. “Why don’t you get one of your trusted detectives to do it?”
“I need someone outside of the force,” said the captain. “Drop the act, Frank. If you don’t know what it means for me to be here, you’re not the person I need.”
Frank chuckled. “A leak? On your force?”
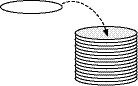
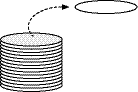
“Worse. Last night someone broke into the station’s record room and stole over 500 scrolls.”
“What were they after?” asked Frank. Without thinking, he leaned forward in his chair and reached for a fresh scroll and a quill. The movement came automatically to him, like drinking coffee or avoiding stairs.
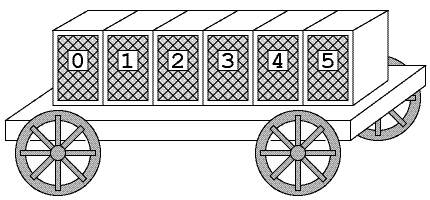
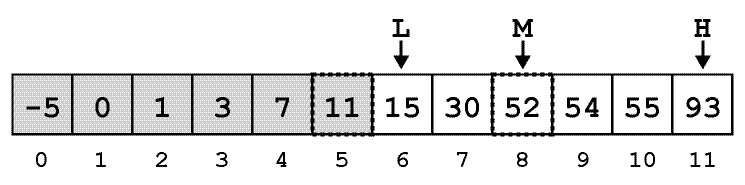
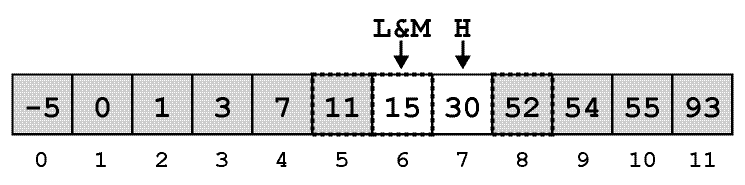
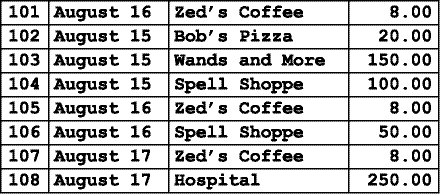
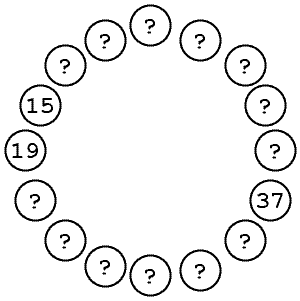
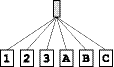
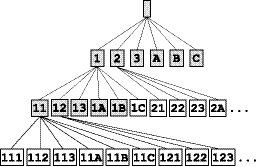
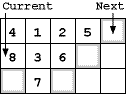
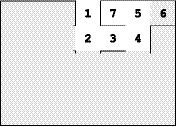
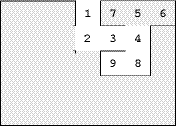
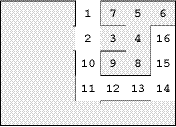
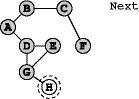
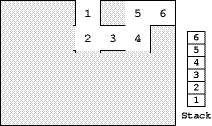
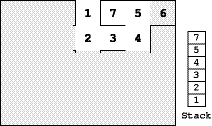
“I don’t know,” said Donovan. “There was no pattern. They stole whole shelves of documents, everything from property disputes to expense reports. They took all the ledgers we keep on assassins, celebrities, private investigators, notaries . . . They even took both boxes of Farmer Swinson’s noise complaints. But other shelves were completely untouched. We counted at least 512 missing documents.”
“Maybe it was one of Farmer Swinson’s neighbors,” joked Frank. “They must’ve heard that after a mere hundred complaints, an intern will come to your house and give you a stern lecture.”
Captain Donovan didn’t bother to reply. He just stared pityingly until Frank cleared his throat and broke the silence. “So you want me to find these documents?”
The captain shook his head. “I want you to find the thieves. We have backups of the documents. I want to know what information they needed and what they plan to do with it.”
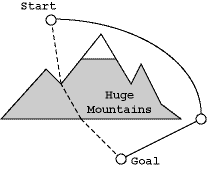
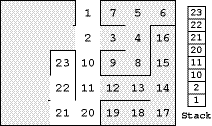
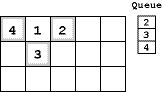
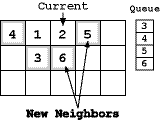
“A search problem,” Frank mused. During his time on the force, his two specialties had been search problems and annoying the captain.
“Does the king know?” Frank asked.
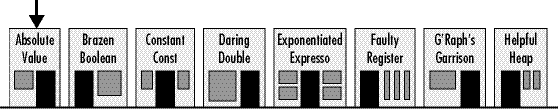
“I briefed him yesterday,” said the captain, a hint of annoyance in his voice. “Ever since the trouble with that crackpot wizard, the king insists on daily briefings on everything.” Two years ago, a megalomaniac wizard named Exponentious had tried to destroy the entire kingdom. Since then King Fredrick had personally instituted sweeping upgrades to the kingdom’s security, with over 300 new security regulations, at least 5 of which dealt with the storage of official documents in government buildings under 10 stories tall.
“I can’t blame him though,” Donovan grumbled. “It was a close call. If it hadn’t been for Princess Ann, who knows where the kingdom would be now.”
Frank nodded silently. Exponentious had attacked the algorithmic foundations of the kingdom by cursing the scholars who studied those algorithms. Within months he had rendered even simple operations inefficient, and the kingdom had started to grind to a halt. Evidence of the damage had been everywhere; even in his local bakery, Frank had himself witnessed panic break out as customers discovered they couldn’t remember how to arrange themselves into a line.
“The king has, of course, taken a personal interest in the matter,” the captain continued irritably. “He wants all the details: Who’s assigned to the case? Which search algorithms are we using? Have we scoured all of the neighboring buildings?”
Frank stifled a chuckle and mulled over the proposition. A consulting gig for the capital’s police force would be good money. He glanced down at his feet, where the tip of a toe peeked through a hole in his shoe. “If I’m going to consult,” he said, “I’m going to do things my way.”
This was the moment of truth. Five years ago he’d been kicked off the force for doing things his way. The captain was a man of rules and order. Frank’s last use of heuristics had been the final straw—Captain Donovan had claimed his badge that very afternoon. But, then again, doing things his own way had always gotten Frank results.
“I figured as much,” the captain responded at last. He pulled a thin folder from under his trench cloak and dropped it on Frank’s desk.
“I’ll be in touch,” Donovan said. Then, without ceremony, he turned and left the office.
Three hours and twelve mugs of coffee later, Frank sat hunched over his desk and thumbed through the thin folder of information for the seventh time. The words jumped and swayed in the flickering candlelight, but didn’t provide any new insights.
There wasn’t a lot to go on. The captain had given him a list of missing documents and the duty roster for the night in question, but nothing more.
Finally, with an exaggerated sigh, Frank grabbed a piece of parchment and started making notes.
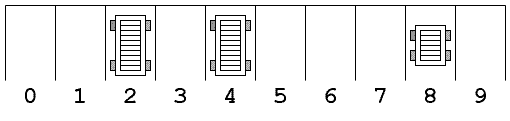
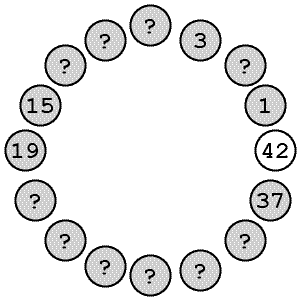
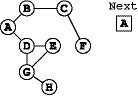
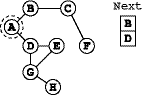
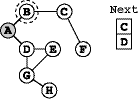
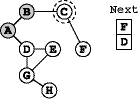
The first step in any search problem is determining what it is you hope to find—the target, as his old instructor in Police Algorithms 101 called it. Frank had learned that lesson early; he’d been tasked in his first week as an officer with finding the duke’s prize stallion, and he’d proudly returned to the station that same afternoon with a 42-pound horned turtle. Apparently, the impressive reptile wasn’t good enough. A good search algorithm means nothing if you’re looking for the wrong thing.
In this case it wasn’t a what, but rather a who. The captain had been right about that point. Once the thieves had the documents, it didn’t matter if the police got them back. The thieves already had whatever information they needed.
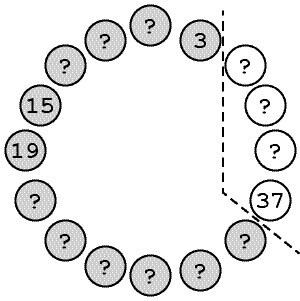
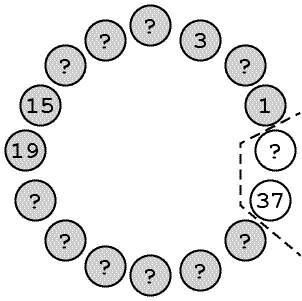
So his target was simple: the person or persons who stole the documents.
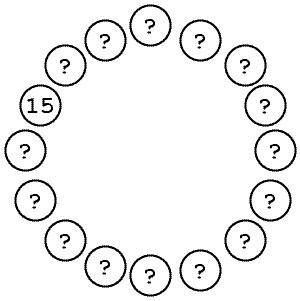
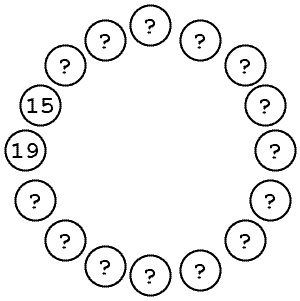
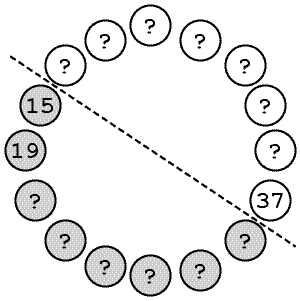
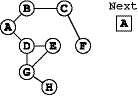
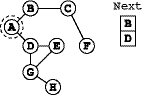
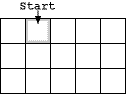
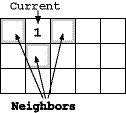
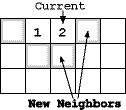
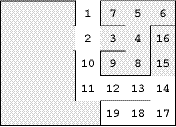
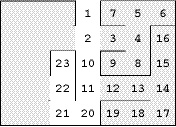
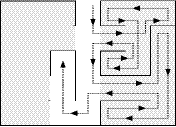
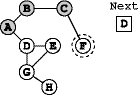
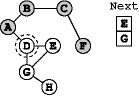
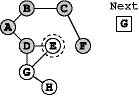
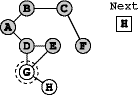
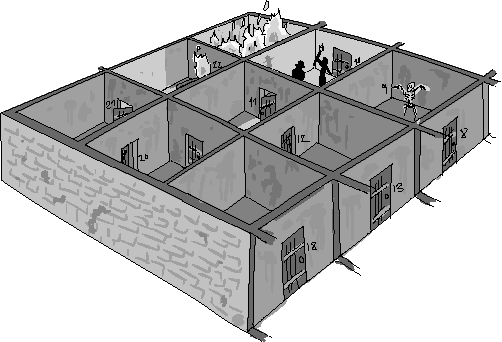
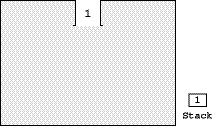
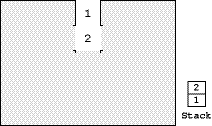
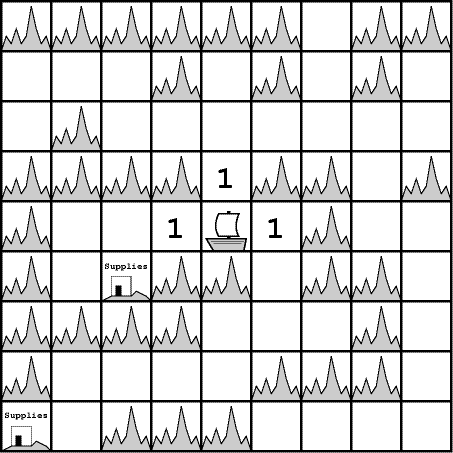
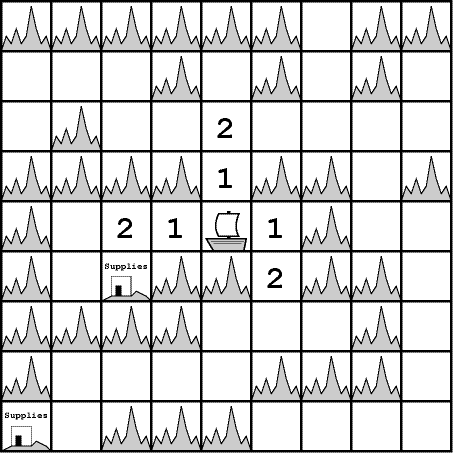
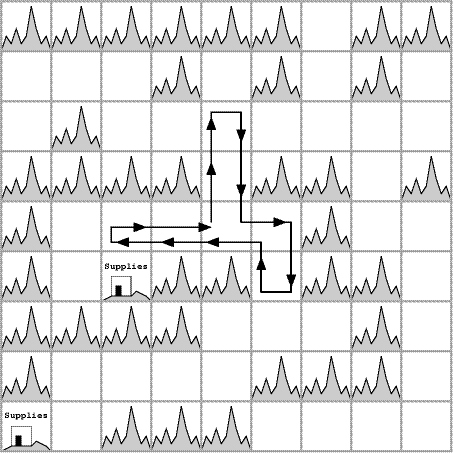
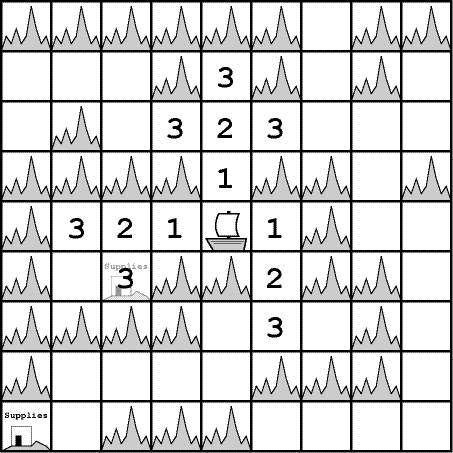
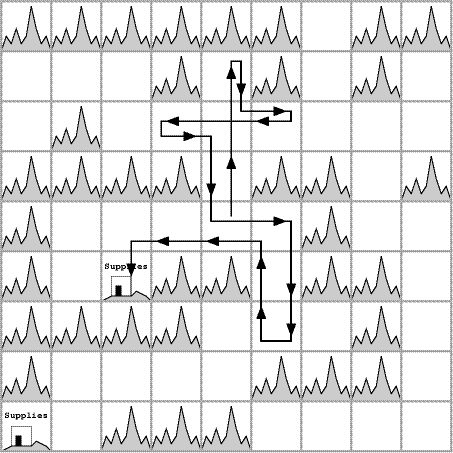
The second step in any search problem is identifying the search space. What are you searching? During Frank’s daily search for his keys, the search space was every flat surface in his office. And when Frank wanted to find a criminal, his search space was every person in the vicinity of the capital.
Frank sat back and rubbed his eyes. It was a big search problem, finding a specific criminal in a city of criminals. But he had seen worse.
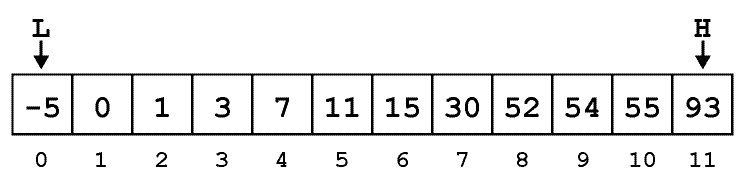
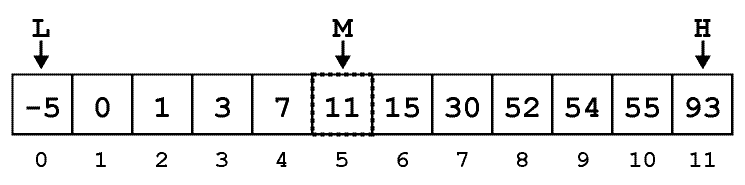
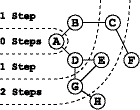
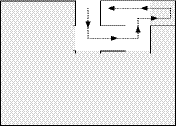
Now that he had defined the problem, he could start on an algorithm. A linear search was out; he couldn’t afford to question everyone in the city. He could also rule out many of the other, fancier algorithms he had studied in the academy. For a problem like this, he would have to go back to his toolkit of basic search algorithms—the private investigator’s most trusted friends.
Frank made a note on the parchment. He had the target to find, he knew the search space, and he had his algorithm. It was time to get to work.